Update: Oct 2019. Leveraging the SailPoint IdentityNow API's is now easier using the SailPoint IdentityNow PowerShell Module.
The SailPoint IdentityNow SaaS product is evolving. I’ve previously posted about integrating with the IdentityNow API’s using PowerShell;
- Leveraging v1, v2 and non-Published SailPoint IdentityNow API’s with PowerShell
- Integrating with SailPoint IdentityNow Private (v1) API’s using PowerShell
- Reporting on SailPoint IdentityNow Identities using the ‘Search’ (Beta) API and PowerShell
IdentityNow now has v3 API’s which are essentially the v2 and non-Published API’s with the added benefit of being able to obtain an oAuth token from a new oAuth Token endpoint. Unlike the v2 process for enabling API integration, v3 currently requires that SailPoint generate and provide you with the ClientID and Secret. This Compass document (at the very bottom) indicates that this will be the preferred method for API access moving forward.
The process to get an oAuth Token the process is;
- Generate Credentials using your IdentityNow Admin Username and Password as detailed in my v1 Private API post
- Lines 1-12
- Use the credentials from the step above in the oAuth token request
- Use the ClientID and Secret as Basic AuthN to the Token endpoint
- Obtain an oAuth Token contained in the resulting $Global:v3Token variable
Authentication Script
Update:
- Line 2 with your Org name
- Line 5 with your Admin Login Name
- Line 6 with your Admin Password
- Line 15 with your SailPoint supplied ClientID
- Line 16 with your SailPoint supplied Secret
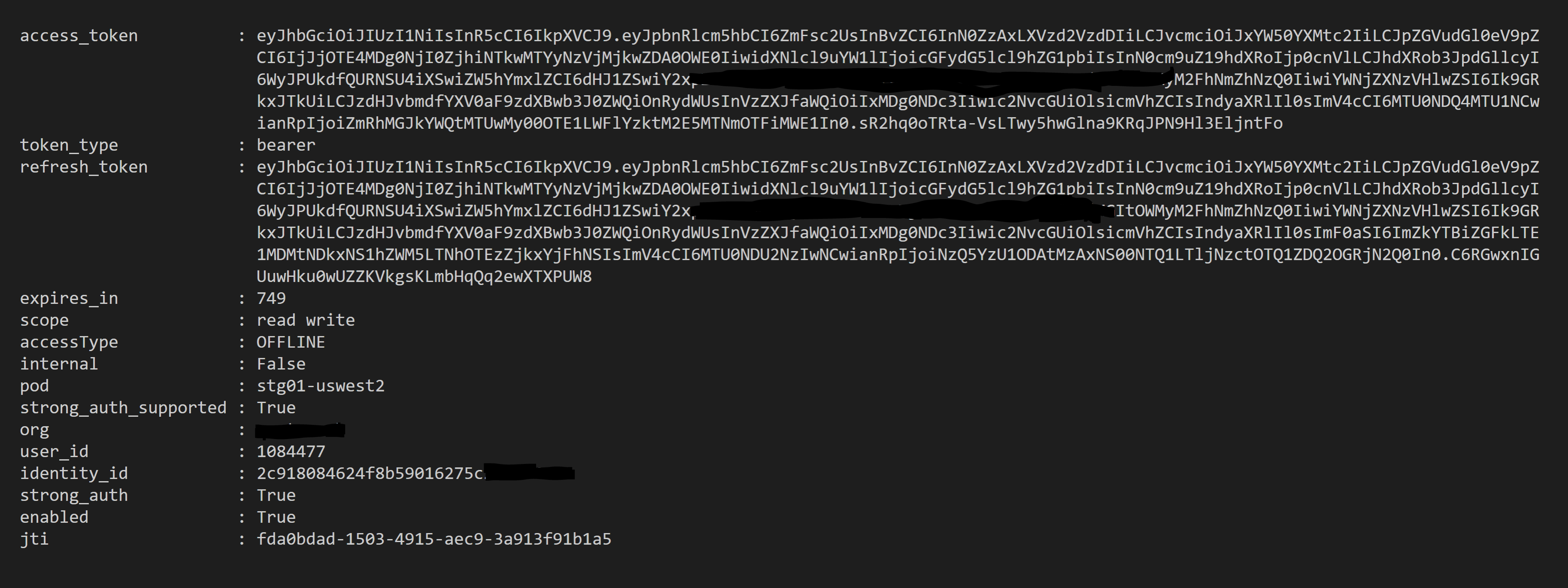
Your resulting token will then look like this;
Using the v3 oAuth Access Token
So far I’ve found that I can use the oAuth Token to leverage the v2 and non-published API’s simply by using the JWT oAuth Token in the Header of the webrequest e.g
@{Authorization = "Bearer $($Global:v3Token.access_token)"}
Depending on which API you are interacting with you may also require Content-Type e.g
@{Authorization = "Bearer $($Global:v3Token.access_token)"; "Content-Type" = "application/json"}
Summary
Talk to your friendly SailPoint Support Rep and get your v3 API ClientID and Secret and discard this previous hack of scraping the Admin Portal for the oAuth Token saving a few hundred lines of code.
