Forefront / Microsoft Identity Manager does not come with an out-of-the-box management agent for managing SharePoint Online.
Whilst the DirSync/AADConnect solution will allow you to synchronise attributes from your On Premise Active Directory to AzureAD, SharePoint only leverages a handful of them. It then has its own set of attributes that it leverages. Many are similarly named to the standard Azure AD attributes but with the SPS- prefix.
For example, here is a list of SPO attributes and a couple of references to associated Azure AD attributes;
- UserProfile_GUID
- SID
- SPS-PhoneticFirstName
- SPS-PhoneticLastName
- SPS-PhoneticDisplayName
- SPS-JobTitle
- SPS-Department
- AboutMe
- PersonalSpace
- PictureURL
- UserName
- QuickLinks
- WebSite
- PublicSiteRedirect
- SPS-Dotted-line
- SPS-Peers
- SPS-Responsibility
- SPS-SipAddress
- SPS-MySiteUpgrade
- SPS-ProxyAddresses
- SPS-HireDate
- SPS-DisplayOrder
- SPS-ClaimID
- SPS-ClaimProviderID
- SPS-ClaimProviderType
- SPS-SavedAccountName
- SPS-SavedSID
- SPS-ResourceSID
- SPS-ResourceAccountName
- SPS-ObjectExists
- SPS-MasterAccountName
- SPS-PersonalSiteCapabilities
- SPS-UserPrincipalName
- SPS-O15FirstRunExperience
- SPS-PersonalSiteInstantiationState
- SPS-PersonalSiteFirstCreationTime
- SPS-PersonalSiteLastCreationTime
- SPS-PersonalSiteNumberOfRetries
- SPS-PersonalSiteFirstCreationError
- SPS-DistinguishedName
- SPS-SourceObjectDN
- SPS-FeedIdentifier
- SPS-Location
- Certifications
- SPS-Skills
- SPS-PastProjects
- SPS-School
- SPS-Birthday
- SPS-Interests
- SPS-StatusNotes
- SPS-HashTags
- SPS-PictureTimestamp
- SPS-PicturePlaceholderState
- SPS-PrivacyPeople
- SPS-PrivacyActivity
- SPS-PictureExchangeSyncState
- SPS-TimeZone
- SPS-EmailOptin
- OfficeGraphEnabled
- SPS-UserType
- SPS-HideFromAddressLists
- SPS-RecipientTypeDetails
- DelveFlags
- msOnline-ObjectId
- SPS-PointPublishingUrl
- SPS-TenantInstanceId
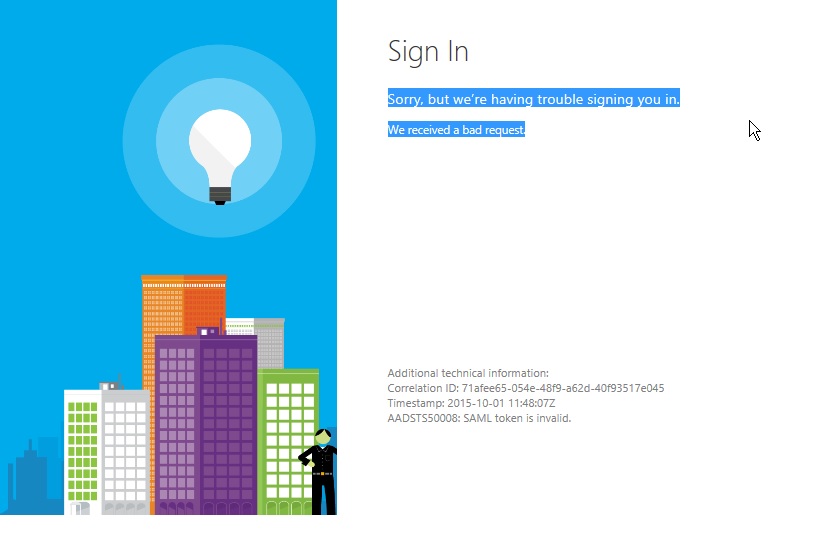
My customer has AADConnect in place that is synchronising their On Premise AD to Office 365.… [Keep reading] “Managing SharePoint Online (SPO) User Profiles with FIM/MIM 2016 and the Granfeldt PowerShell MA”