Microsoft have announced a new method of doing what I describe in this blog post. Matt Shadbolt from the Intune Engineering team has a nice blog post that describe how to use this new process, based on Intune MAM policies. The below information is still useful though if you want to do more specific restrictions (e.g. iOS vs Android native clients).
What is Intune Conditional Access?
Intune Conditional Access is a pretty neat feature that allows administrators to enforce compliance policies to devices prior to allowing them access to sync their mail with Exchange Online. The requirements and process required to implement his feature is quite well documented within Microsoft’s TechNet library: Manage email access with Microsoft Intune
In short, what is happening is Microsoft Intune becomes an additional ‘gate’ that’s sits in front of Exchange Online (or Exchange On-Prem via a connector) that requires devices to provide information on its state (e.g. is it registered, managed or compliant) before being allowed through as part of the authentication process. In its current state, this conditional access feature, for Exchange Online, can supports ‘controlling’ access for clients on mobile devices (i.e. ActiveSync), while for PCs (i.e. Outlook Desktop) and browser based access (i.e. OWA) this is currently in preview.
How Intune Conditional Access works with Mobile Devices with ActiveSync
For mobile devices, ActiveSync is the primary protocol that is used to communicate with Exchange Online and sync the mail to the devices, however it must be noted that there are some variations to how the ActiveSync protocol is implemented. Most users are familiar with what we call the ‘Native mail client’ on iOS and Android devices and more recently now the Outlook for iOS/Android App. While both of these utilise ActiveSync, the defining feature of the Outlook App is that it also supports Modern Authentication which is important for the purposes of this blog. Pretty much all other mail clients utilise ActiveSync with ‘Basic’ authentication which, in simple terms means that they only know to send the username/password to Exchange Online and expect to be let through. They certainly don’t understand the concept of ‘device compliance’ tokens and other features like Multi-Factor Authentication.
To work around this, Intune Conditional Access takes over and leverages the ActiveSync policies feature of Exchange Online to quarantine these “legacy” ActiveSync clients after they have configured their mail profile and injects a fake email into their inbox indicating that they’ve detected the device as being unmanaged and hence does not meet compliance policies to satisfy the conditional access requirements. This email then directs the user to enrol and uplift their device to meet the compliancy policy (e.g. PIN locked, not jail broken etc.) before they are allowed to sync.

The key take-away from this is that Intune Conditional Access is tightly integrated with the ‘Active Sync Policies’ feature of Exchange Online
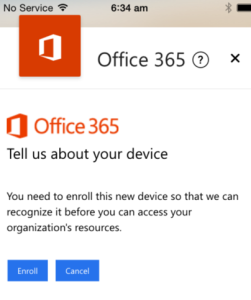
For applications that support Modern Authentication however (i.e. Outlook app), the process is a bit more elegant in that the device compliance (and subsequent enrolment processes) are all performed as part of the authentication / sign in procedure. This is also the same process where MFA prompts can also be initiated.

How to enforce the Outlook App when Intune Conditional Access is used
With that bit of backstory covered off, we can now proceed to explain how you would go about configuring the enforcement of the use of the Outlook App with Intune Conditional Access. There are numerous reasons why you might want to enforce the use of the Outlook App, but some of the key reasons we often see are:
- ActiveSync mail clients do not support ‘Selective Wipe’ if the email profile is not managed by Intune. Intune can only manage iOS native mail app profiles. This leaves Android and third party apps open to data leakage if an employee departs the company with a BYOD device for example (and thus a full wipe is not allowed)
- ActiveSync mail clients using ‘basic authentication’ cannot support Multi Factor Authentication and thus must use the less secure ‘app passwords’ approach
- Only the Outlook App, to date, supports Mobile Application Management (MAM) Intune policies, which is a feature that provides Data Loss Protection functionality by keeping company data within ‘managed’ apps
Within Intune, the below image shows what the standard conditional access policy configuration would look like:

The section highlighted in green is what triggers all ‘Modern Auth’ applications to abide by Intune’s Conditional Access rules. This includes Outlook for desktop and the Outlook for iOS/Android app. The section highlighted in red is what controls Intune Conditional Access for all the ‘legacy’ ActiveSync mail clients (i.e. your native mail clients and third party apps). In order to enforce the use of the Outlook app, we actually have to disable Intune Conditional Access for Exchange ActiveSync apps that use basic authentication.
This may seem weird, but the reason we are doing this is because in order to control what specific ActiveSync clients are allowed to connect to Exchange Online we have to use the Exchange Active Sync Policies feature. Specifically, we have to configure the Access Rules to block all device families and only allow the Outlook App device family, like below:

As noted earlier, when Intune Conditional Access is in play, it actually leverages and takes ownership of this feature, and thus any rules you have configured through that are ignored if the user falls within management under Intune and that conditional access policy is enabled. So, in effect what we are doing is this:
- Enable Intune Conditional Access, but only for ‘Modern Authentication’ Apps. Do not perform the conditional access checks for ‘legacy’ ActiveSync clients
- Configure Exchange Online to block all ActiveSync device clients except the Outlook app
The net effect of doing this is as follows:
- ‘Legacy’ ActiveSync clients will successfully authenticate but their mail synching is blocked by the access rules configured within Exchange Online
- Outlook App clients, even though they are still using ActiveSync, still abide by Intune Conditional Access policies because they are using Modern Auth and can successfully connect to Exchange Online after they meet compliance
The next challenge of course is then convincing all your users to stop using their Native Mail Client (or their preferred third party app) and use the Outlook app instead, but that’s a post for another day/

