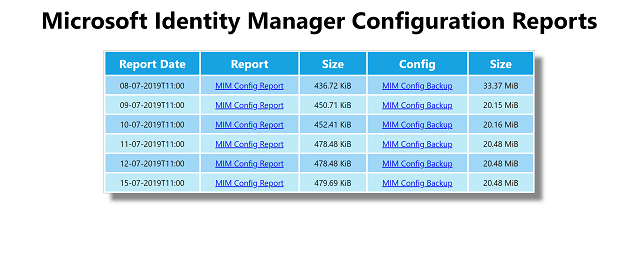
Automated Microsoft Identity Manager Configuration Backups & Documentation to Azure
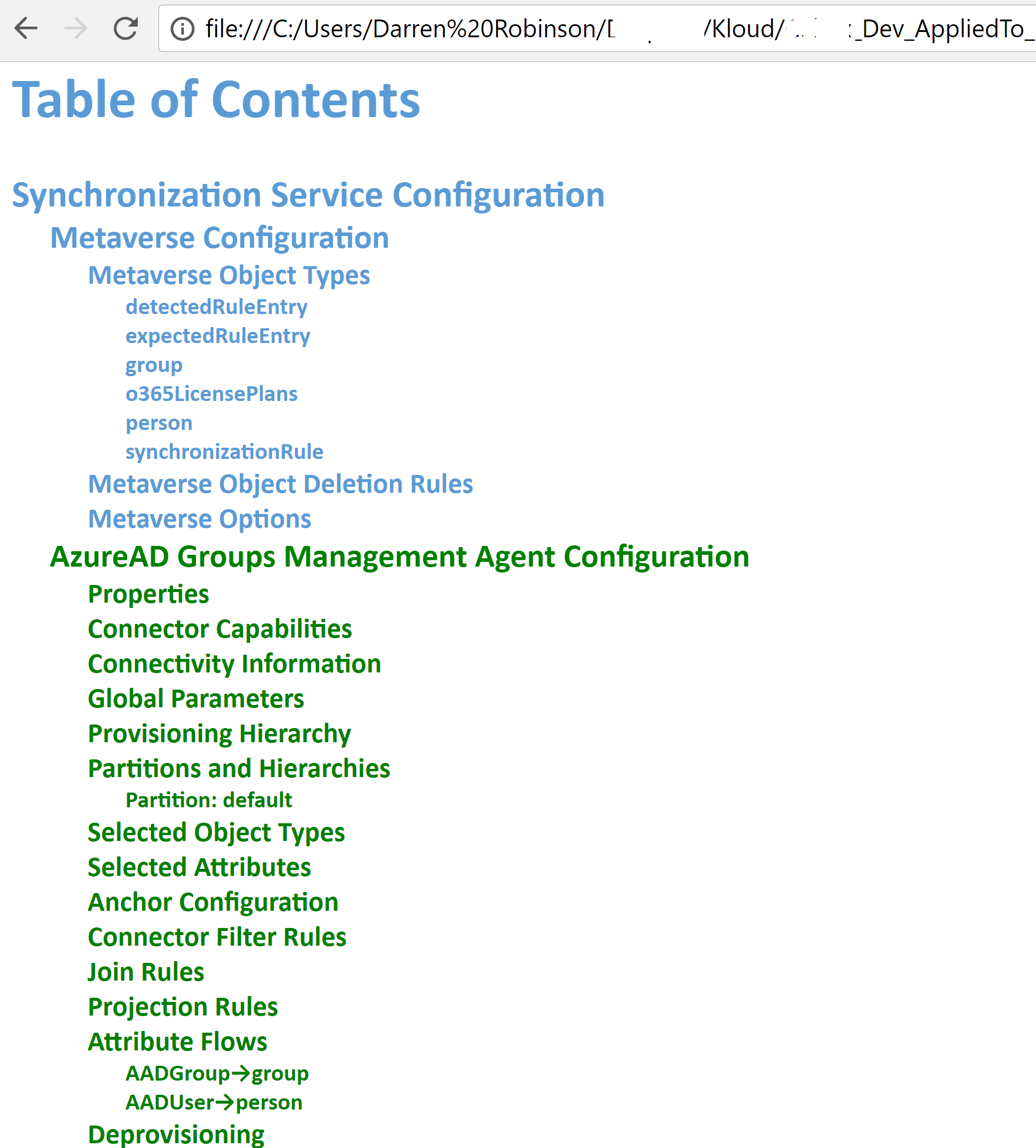
Two and half years ago I wrote this post on creating an Azure Function to trigger the process of Automating Microsoft Identity Manager Configuration backups. The Azure Function piece was a little obtuse. I was using it, as it was the “new thing” and it was my new hammer. And everything was a nail. The reality is that the rest of the process is completely valid (nightly backups of your development Identity Manager configuration).… [Keep reading] “Automated Microsoft Identity Manager Configuration Backups & Documentation to Azure”