Stacking the AWS CloudFormation
Automate your Cloud Operations blog post Part 1 have given us the basic understanding on how to automate the AWS stack using CloudFormation.
This post will help the reader on how to layer the stack on top of the existing AWS CloudFormation stack using AWS CloudFormation instead of modifying the base template. AWS resources can be added into existing VPC using the outputs detailing the resources from the main VPC stack instead of having to modify the main template.
This will allow us to compartmentalize, separate out any components of AWS infrastructure and again versioning all different AWS infrastructure code for every components.
Note: The template I will use for this post for educational purposes only and may not be suitable for production workloads :).
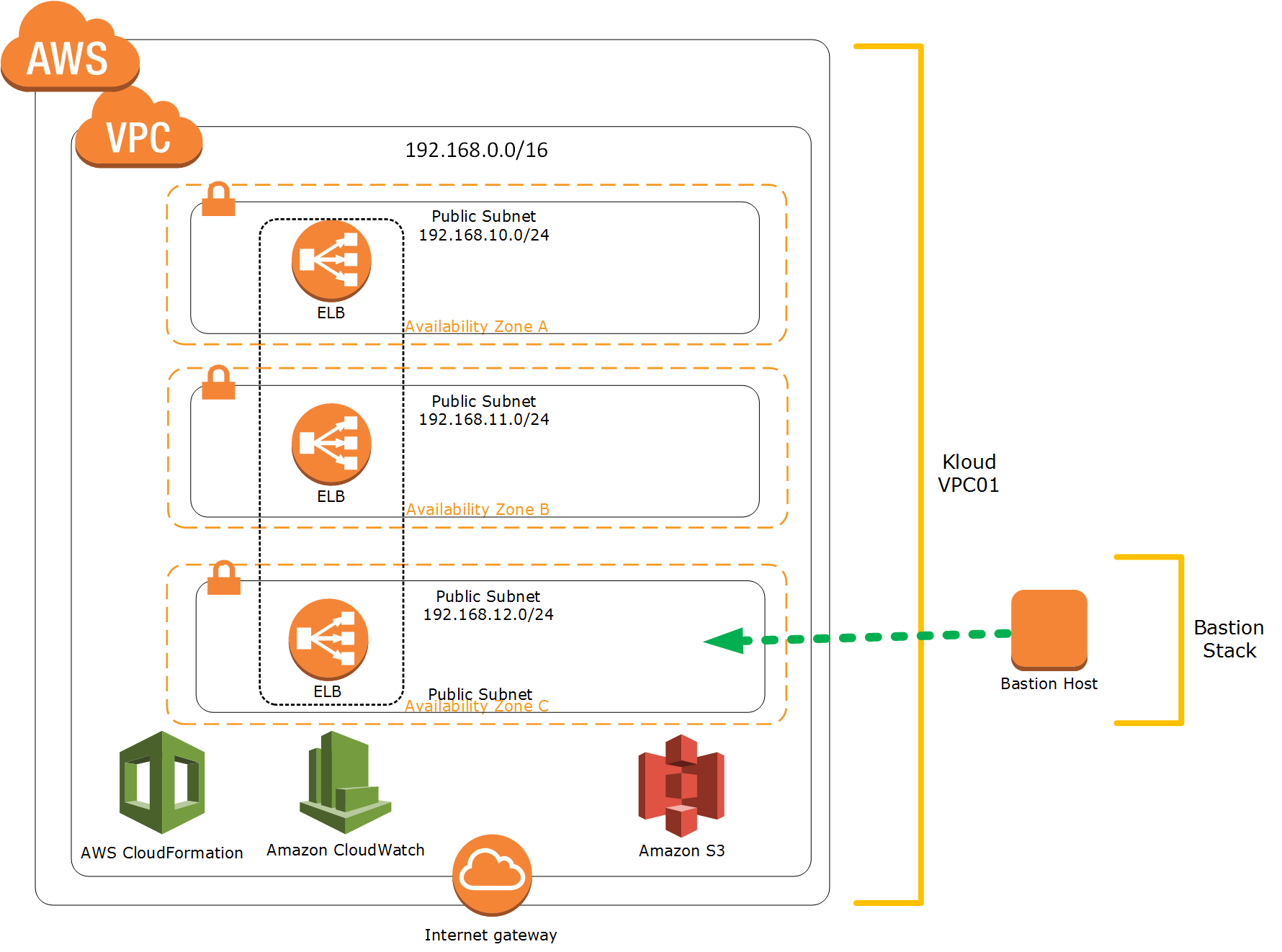
Diagram below will help to illustrate the concept:
Bastion Stack
Previously (Part 1), we created the initial stack which provide us the base VPC. Next, we will provision bastion stack which will create a bastion host on top of our base VPC. Below are the components of the bastion stack:
- Create IAM user that can find out information about the stack and has permissions to create KeyPairs and actions related.
- Create bastion host instance with the AWS Security Group enable SSH access via port 22
- Use CloudFormation Init to install packages, create files and run commands on the bastion host instance also take the creds created for the IAM user and setup to be used by the scripts
- Use the EC2 UserData to run the cfn-init command that actually does the above via a bash script
- The condition handle: the completion of the instance is dependent on the scripts running properly, if the scripts fail, the CloudFormation stack will error out and fail
Below is the CloudFormation template to build the bastion stack:
Following are the high level steps to layer the bastion stack on top of the initial stack:
- Get the subnet details which we created previously on initial stack
- Download the bastion stack template: https://s3-ap-southeast-2.amazonaws.com/andreaswasita/cloudformation_template/demo/lab1-bastion_stack.template
- Create new stack on AWS CloudFormation and specify the initial stack VPC ID, SubnetId, KeyName and BastionKey Name in the related parameters
- Tags the instance
- Next we need to connect and validate the bastion host instance also “cat” out the bastion keypair. You can use PuTTY or Git Bash for Windows users or OSX Terminal for OSX users.
I put together the following video on how to use the template:
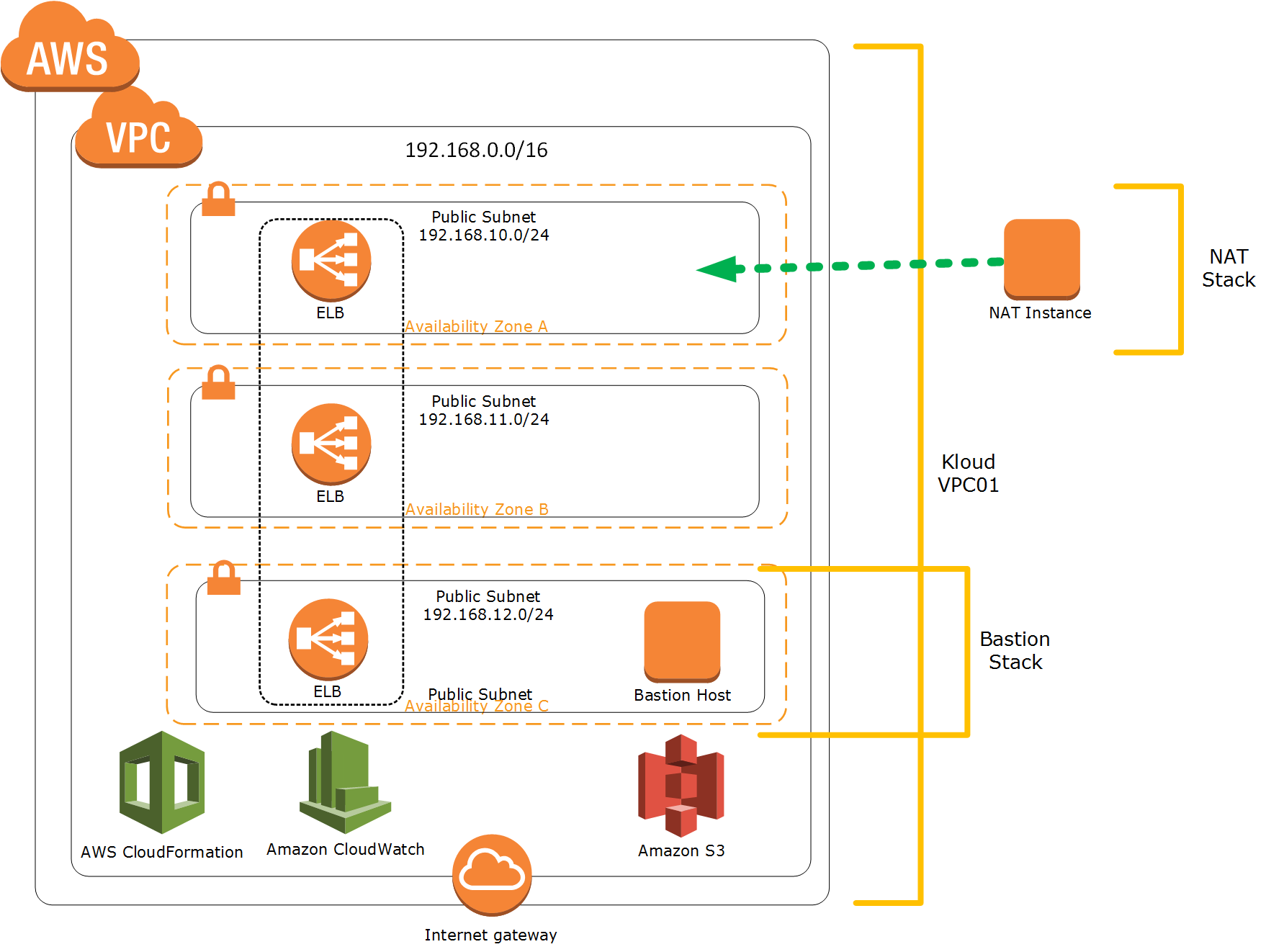
NAT Stack
It is important to design the VPC with security in mind. I recommend to design your Security Zone and network segregation, I have written a blog post regarding how to Secure Azure Network. This approach also can be impelemented on AWS environment using VPC, subnet and security groups. At the very minimum we will segregate the Private subnet and Public subnet on our VPC.
NAT instance will be added to our Initial VPC “public” subnets so that the future private instances can use the NAT instance for communication outside the Initial VPC. We will use exact same method like what we did on Bastion stack.
Diagram below will help to illustrate the concept:
The components of the NAT stack:
- An Elastic IP address (EIP) for the NAT instance
- A Security Group for the NAT instance: Allowing ingress traffic tcp, udp from port 0-65535 from internal subnet ; Allowing egress traffic tcp port 22, 80, 443, 9418 to any and egress traffic udp port 123 to Internet and egress traffic port 0-65535 to internal subnet
- The NAT instance
- A private route table
- A private route using the NAT instance as the default route for all traffic
Following is the CloudFormation template to build the stack:
Similar like the previous steps on how to layer the stack:
- Get the details on public subnet to put the NAT instance in
- Download the NAT stack template: https://s3-ap-southeast-2.amazonaws.com/andreaswasita/cloudformation_template/demo/lab1-nat_stack.template
- Create new stack on AWS CloudFormation and specify the initial stack VPC ID, SubnetId, KeyName and BastionKey Name in the related parameters
- Tags as usual
Hopefully after reading the Part 1 and the Part 2 of my blog posts, the readers will gain some basic understanding on how to automate the AWS cloud operations using AWS CloudFormation.
Please contact Kloud Solutions if the readers need help with automating AWS production environment
www.wasita.net