When you have a large Azure AD tenant it is likely that you want to scope your SailPoint IdentityNow Source based on the different type of identities it contains. Using the Filtering and Scoping section of the Azure AD Source Configuration Guide from Compass I first started constructing queries as I normally would with Azure AD against the Microsoft Graph API.
However the queries/filters I was using against Microsoft Graph were not working for the Azure AD IdentityNow Source. On aggregation the Source Connector would throw errors such as;
….java.lang.RuntimeException – sailpoint.connector.ConnectorException: Exception occurred. Error message – Exception occurred in processReadRequest. Error – Response Code – 400 Error – Bad Request Property ‘msGraphAADAttribute’ does not exist as a declared property or extension property…..
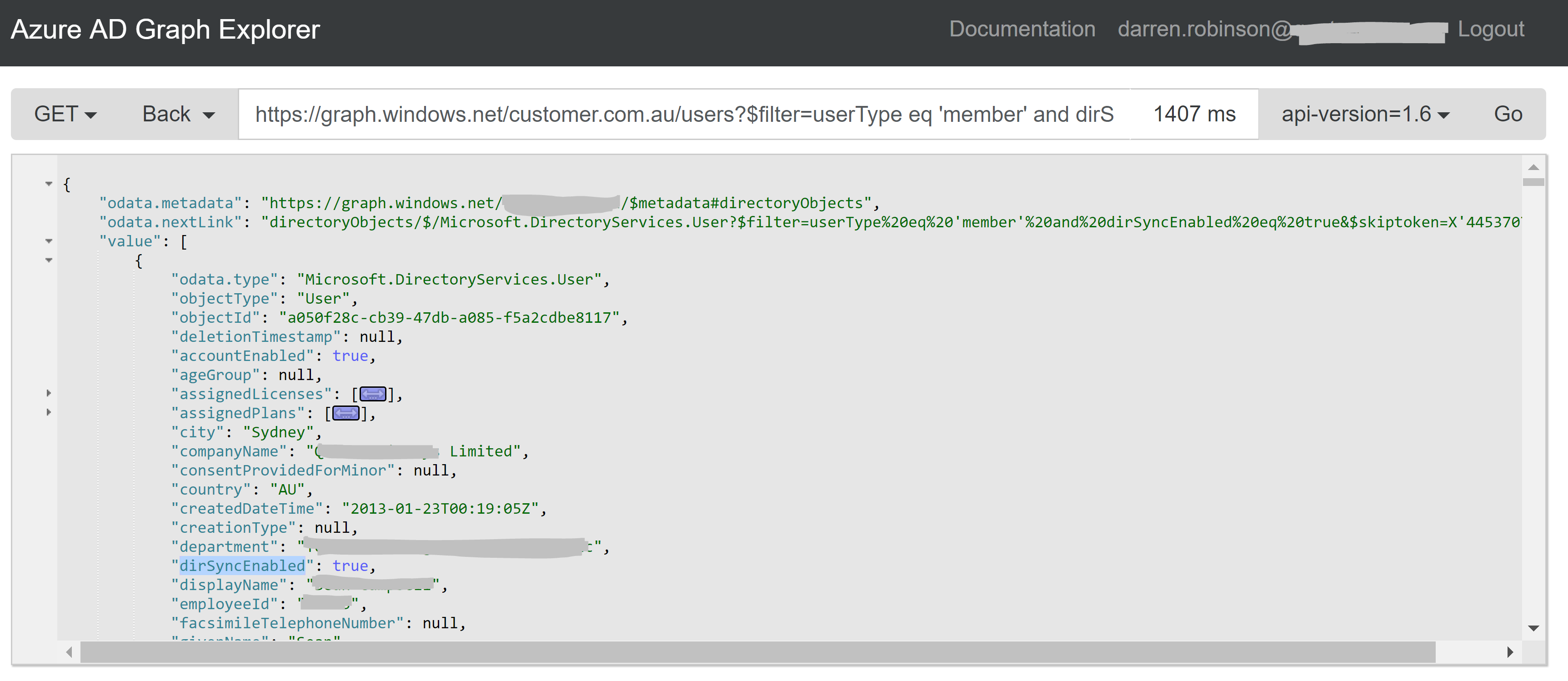
Following some discussions with the IdentityNow Professional Services guys I learned that the IdentityNow Azure AD Source Connector uses the Azure AD v1 Graph API endpoint.
With this information I was then able to use the Azure Active Directory v1 Graph API Explorer to develop queries that would then work for ‘User Filters’. This is extremely quick and useful. For guidance on using Azure AD Filters this Microsoft document will get you started.
Configuring Azure AD Source Filters
To configure Source Filters for the IdentityNow Azure AD Source I use PowerShell as per the many IdentityNow Configuration and Automation posts I’ve previous written.
SailPoint IdentityNow Authentication
The script snippets below just show the commands to create three different Azure AD Source Filters (if you need all three like me you will need to configure three separate Sources with a different filter on each). In order to utilise these you will need to be authenticated to the SailPoint IdentityNow API. This post details connecting to the SailPoint IdentityNow v3 API endpoint using PowerShell.
Below shows three snippets for scoping the Azure AD Source down to specific User Types;
- AAD Guest Accounts (B2B)
- AAD Hybrid Accounts (On Premise AD and Azure AD)
- AAD Cloud Only Accounts
To update a source you send a POST request to the Update Source API where yourOrg is your Tenant Org Name and SourceNumber is the number of the Source to update (e.g. 12345). The body is the connector_userFilters attribute with the value for the filter.
https://yourOrg.api.identitynow.com/cc/api/source/update/SOURCENumber
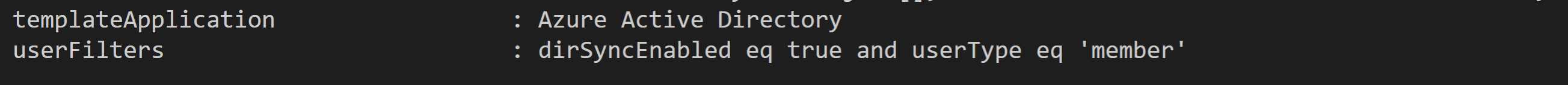
Hybrid Accounts
The following shows the tail of the output from the returned object after updating the Source for a filter for Azure AD Hybrid Accounts;
dirSyncEnabled eq true and userType eq 'member'
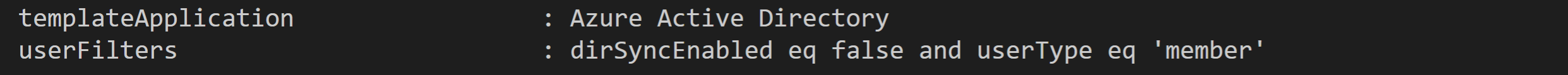
Azure AD Cloud Only Accounts
The following shows the tail of the output from the returned object after updating the Source for a filter for Azure AD Cloud Only Accounts;
dirSyncEnabled eq false and userType eq 'member'
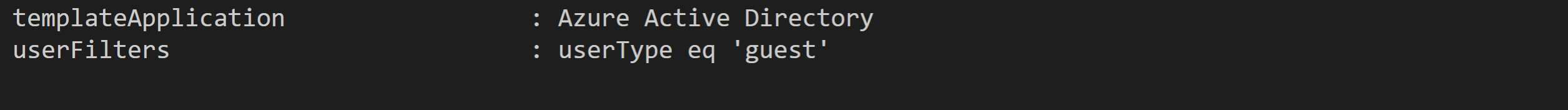
Azure AD Guest (B2B) Accounts
The following shows the tail of the output from the returned object after updating the Source for a filter for Azure AD Cloud Only Accounts;
userType eq 'guest'
Summary
Knowing the API the IdentityNow Azure AD Source is using allows us to construct filters to scope the Azure AD Source to the specific users for an implementation.
