One of the benefits of an Active Directory (AD) running with only Windows Server 2012 domain controllers is the use of ‘Group Managed Service Accounts’ (GMSAs).
GMSAs can essentially execute applications and services similar to an Active Directory user account running as a ‘service account’. GMSAs store their 120 character length passwords using the Key Distribution Service (KDS) on Windows Server 2012 DCs and periodically refresh these passwords for extra security (and that refresh time is configurable).
This essentially provides the following benefits:
- Eliminates the need for Administrators to store static service accounts passwords in a ‘password vault’
- Increased security as the password is refreshed automatically and that refresh interval is configurable (you can tell it to refresh the password every day if you want to.
- The password is not known even to administrators so there is no chance for attackers to try to hijack the GMSA account and ‘hide their tracks’ by logging in as that account on other Windows Servers or applications
- An extremely long character password which would require a lot of computing power & time to break
There is still overhead in using GMSA versus a traditional AD user account:
- Not all applications or services support GMSA so if the application does not document their supportability, then you will need to test their use in a lab
- Increase overhead in the upfront configuration getting them working and testing versus a simple AD user account creation
- GMSA bugs (see Appendix)
I recently had some time to develop & run a PowerShell script under Task Scheduler, but I wanted to use GMSA to run the job under a service account whose password would not be known to any administrator and would refresh automatically (every 30 days or so).
There are quite a few blogs out there on GMSA, including this excellent PFE blog from MS from 2012 and the official TechNet library.
My blog is really a ‘beginners guide’ to GMSA in working with it in a simple Task Scheduler scenario. I had some interesting learnings using GMSA for the first time that I thought would prove useful, plus some sample commands in other blogs are not 100% accurate.
This blog will run through the following steps:
- Create a GMSA and link it to two Windows Servers
- ‘Install’ the GMSA on the Windows Servers and test it
- Create a Task Schedule job and have it execute it under the GMSA
- Execute a GMSA refresh password and verify Task Schedule job will still execute
An appendix at the end will briefly discuss issues I’m still having though running a GMSA in conjunction with an Active Directory security group (i.e. using an AD Group instead of direct server memberships to the GMSA object).
A GMSA essentially shares many attributes with a computer account in Active Directory, but it still operates as a distinct AD class object. Therefore, its use is still quite limited to a handful of Windows applications and services. It seems the following apps and services can run under GMSA but I’d first check and test to ensure you can run it under GMSA:
- A Windows Service
- An IIS Application Pool
- SQL 2012
- ADFS 3.0 (although the creation and use of GMSA using ADFS 3.0 is quite ‘wizard driven’ and invisible to admins)
- Task Scheduler jobs
This blog will create a GMSA manually, and allow two Windows Servers to retrieve the password to that single GMSA and use it to operate two Task Schedule jobs, one per each server.
Step 1: Create your KDS root key & Prep Environment
A KDS root key is required to work with GMSA. If you’re in a shared lab, this may already have been generated. You can check with the PowerShell command (run under ‘Run As Administrator’ with Domain Admin rights):
Get-KDSrootkey
If you get output similar to the following, you may skip this step for the entire forest:
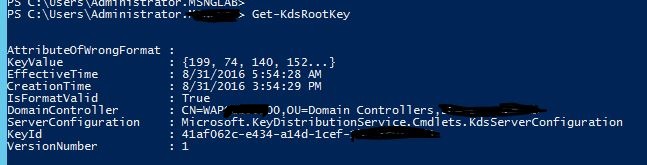
If there is no KDS root key present (or it has expired), the command to create the KDS root key for the entire AD forest (of which all GMSA derive their passwords from) is as follows:
Add-KDSRootKey –EffectiveImmediately
The ‘EffectiveImmediately’ switch is documented that may need to wait up to 10 hours for it to take effect to take into account Domain Controller replication. however you can speed up the process (if you’re in a lab) by following this link.
The next few steps will assume you have the following configured:
- Domain Admins rights
- PowerShell loaded with ‘Run as Administrator’
- Active Directory PowerShell module loaded with command:
- import-module activedirectory
Step 2: Create a GMSA and link it to two (or more) Windows Servers
This step creates the GMSA object in AD, and links two Windows Servers to be able to retrieve (and therefore login) as that GMSA on those servers to execute the Task Schedule job.
The following commands will :
$server1 = Get-ADComputer <Server1 NETBIOS name>
$server2 = Get-ADComputer <Server2 NETBIOS name>
New-ADServiceAccount -name gmsa-pwdexpiry -DNSHostName gmsa-pwdexpiry.domain.lab -PrincipalsAllowedToRetrieveManagedPassword $server1,$server2
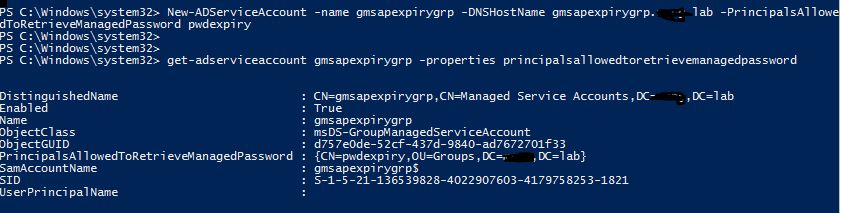
Get-ADServiceAccount -Identity gmsa-pwdexpiry -Properties PrincipalsAllowedToRetrieveManagedPassword
You should get an output similar to the following:
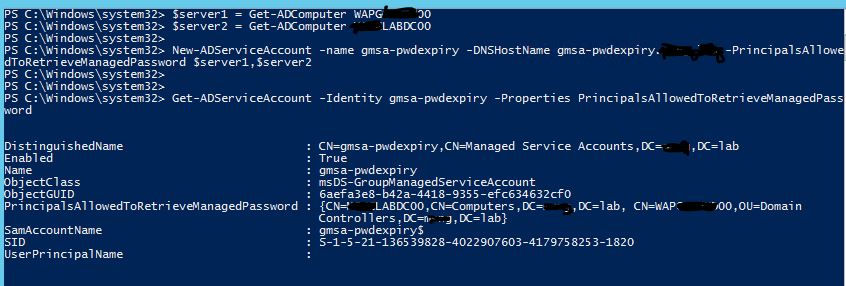
The important verification step is to ensure the ‘PrincipalsAllowed…’ value contains all LDAP paths to the Windows Servers who wish to use the GMSA (the ones specified as variables).
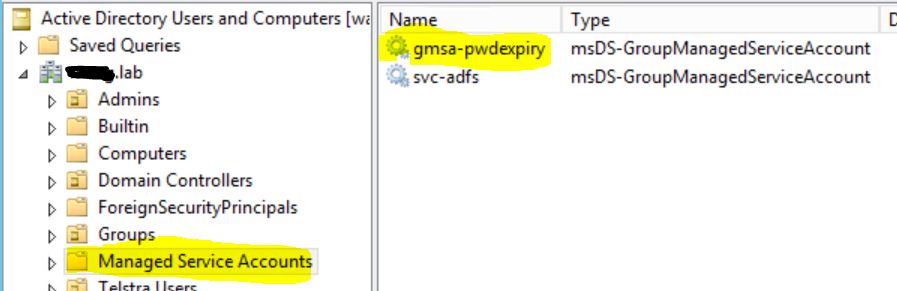
The GMSA object will get added by default to the ‘Managed Service Accounts’ container object in the root of the domain (unless you specify the ‘-path’ switch to tell it to install it to a custom OU).
Notes:
- To reiterate, many blogs point out that you can use the switch: ‘PrincipalsAllowedToRetrieveManagedPassword’ (almost the longest switch name I’ve ever encountered!) to specify an ‘AD group name’. I’m having issues with using that switch to specify an and work with an AD group instead of direct computer account memberships to the GMSA. I run through those issues in the Appendix.
- A lot of blogs just state you can just specify the server NETBIOS names for the ‘principals’ switch, however I’ve found you need to first retrieve the AD objects first using the ‘get-ADcomputeraccount’ commands
- I did not specify a Service Principal Name (SPN) as my Task Scheduler job does not require one, however be sure to do so if you’re executing an application or service requiring one
- I accepted the default password refresh interval of 30 days without specifying a custom password refresh interval (viewable in the attribute value: ‘msDS-ManagedPasswordInterval’). Custom refresh intervals can only be specified during GMSA creation from what I’ve read (a topic for a future blog!).
- Be sure to specify a ‘comma’ between the two computer account variables without a space
OPTIONAL Step 2A: Add or Removing Computers to the GMSA
If you’ve created the GMSA but forgot to add a server account, then to modify the server computer account membership of a GMSA, I found the guidance from MS a little confusing. In my testing I found you cannot really add or remove individual computers to the GMSA without re-adding every computer back into the membership list.
You can use this command to update an existing GMSA, but you will still need to specify EVERY computer that should be able to retrieve the password for that GMSA.
For example, if I wanted to add a third server to use the GMSA I would still need to re-add all the existing servers using the ‘Set-ADServiceAccount’ command:
$server1 = Get-ADComputer <Server1 NETBIOS name>
$server2 = Get-ADComputer <Server2 NETBIOS name>
$server3 = Get-ADComputer <Server3 NETBIOS name>
Set-ADServiceAccount -Identity gmsa-pwdexpiry -PrincipalsAllowedToRetrieveManagedPassword $server1,$server2,$server3
(Also another reason why I want to work with an AD group used instead!)
Step 3: ‘Install’ the Service Account
According to Microsoft TechNet, the ‘Install-ADServiceAccount’ “makes the required changes locally that the service account password can be periodically reset by the computer”.
I’m not 100% sure what these changes are local to the Windows Server, but after you run the command, the Windows Server will have permission to reset the password to the GMSA.
You run this command on a Windows Server (who should already be in the list of ‘PrincipalsAllowed…’ computer stored in the GMSA):
Install-ADServiceAccount gsma-pwdexpiry
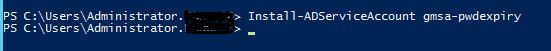
After you run this command, verify that both the ‘PrincipalsAllowed…’ switch and ‘Install’ commands are properly configured for this Windows Server:
Test-ADServiceAccount gsma-pwdexpiry
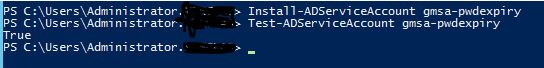
A value of ‘True’ for the Test command means that this server can now use the GMSA to execute the Task Scheduler. A value of ‘False’ means that either the Windows Server was not added to the ‘Principals’ list (using either ‘New-ADServiceAccount’ or ‘Set-ADServiceAccount’) or the ‘Install-ADServiceAccount’ command did not execute properly.
Finally, in order to execute Task Scheduler jobs, be sure also to add the GSMA to the local security policy (or GPO) to be assigned the right: ‘Log on as batch job’:
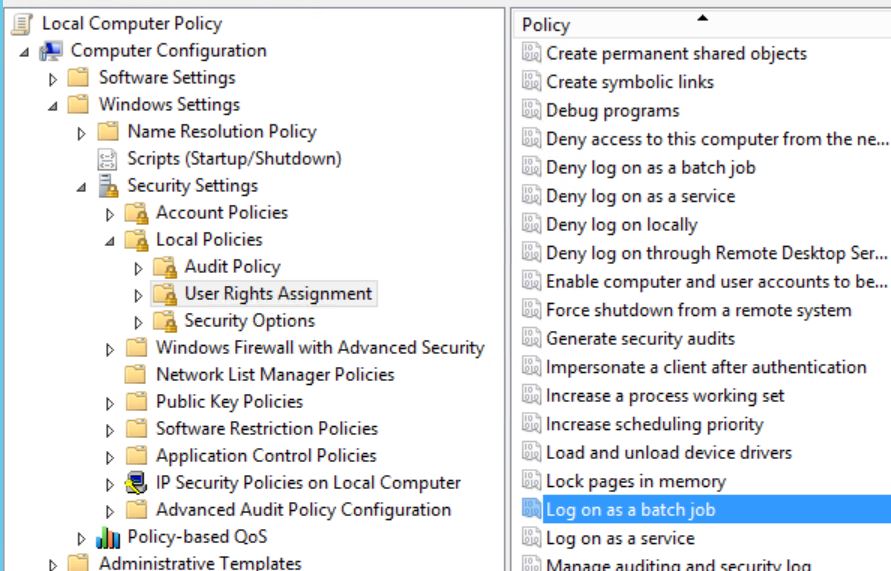
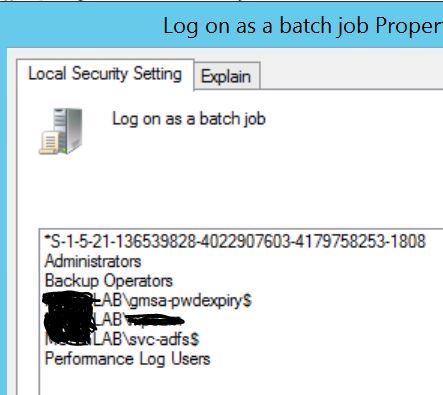
Without this last step, the GMSA account will properly login to the Windows Server but the Task Scheduler job will not execute as the GMSA will not have the permission to do so. If the Windows Server is a Domain Controller, then you will need to use a GPO (either ‘Default Domain Controller’ GPO or a new GPO).
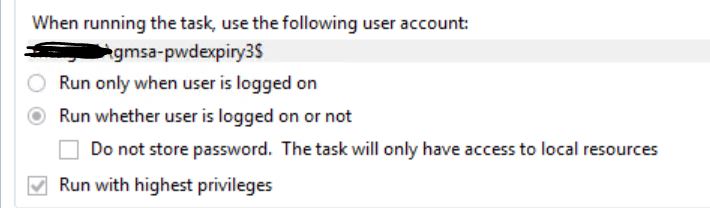
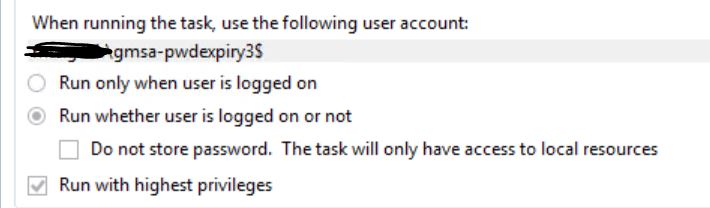
Step 4: Create the Task Schedule Job to run under GMSA
Windows Task Scheduler (at least on Windows Server 2012) does not allow you to specify a GMSA using the GUI. Instead, you have to create the Task Schedule job using PowerShell. The password prompt when you create the job using the GUI will ask you to specify a password when you go to save it (which you will never have!)
The following four commands will instead create the Task Schedule job to execute an example PowerShell script and specifies the GMSA object to run under (using the $principal object):
$action = New-ScheduledTaskAction powershell.exe -Argument “-file c:\Scripts\Script.ps1” -WorkingDirectory “C:\WINDOWS\system32\WindowsPowerShell\v1.0”
$trigger = New-ScheduledTaskTrigger -At 12:00 -Daily
$principal = New-ScheduledTaskPrincipal -UserID domain.lab\gmsa-pwdexpiry$ -LogonType Password -RunLevel highest
Register-ScheduledTask myAdminTask –Action $action –Trigger $trigger –Principal $principal
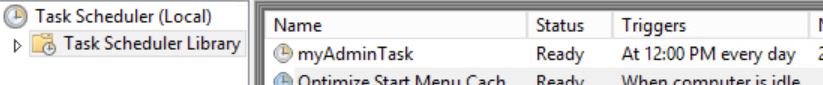
Note:
- Be sure to replace the ‘domain.lab’ with the FQDN of your domain and other variables such as script path & name
- It’s optional to use the switch: ‘-RunLevel highest’. This just sets the job to ‘Run with highest privileges’.
- Be sure to specify a ‘$’ symbol after the GMSA name for the ‘-UserID’. I also had to specify the FQDN instead of the NETBIOS for the domain name as well.
Step 5: Kick the tyres! (aka test test test)
Yes, when you’re using GMSA you need to be confident that you’re leaving something that is going to work even when the password expires.
Some common task that I like to perform to verify the GMSA is running include:
Force the GMSA to password change:
You can force the GMSA to reset it’s password by running the command:
Reset-ADServiceAccountPassword gmsa-pwdexpiry
You can then verify the time date of the last password set by running the command:
Get-ADServiceAccount -Identity gmsa-pwdexpiry -Properties passwordlastset
The value will be next to the ‘PasswordLastSet’ field:
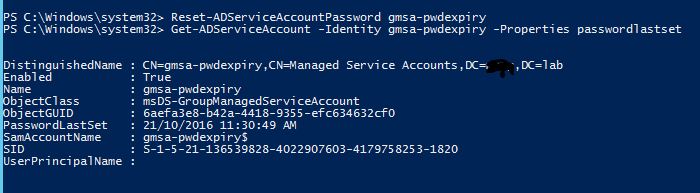
After forcing a password reset, I would initiate a Task Schedule job execution and be sure that it operates without failure.
Verify Last Login Time
You can also verify that the GMSA is logging in properly to the server by checking the ‘Last Login value’:
Get-ADServiceAccount -Identity gmsa-pwdexpiry -Properties LastLogonDate
View all Properties
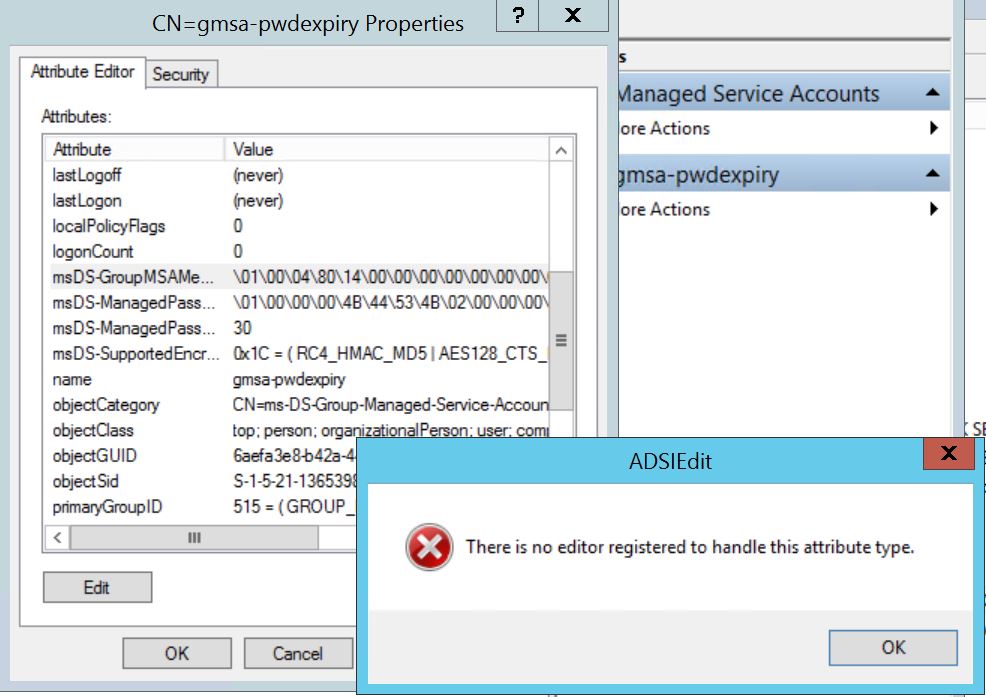
Finally, if you’re curious as to what else that object stores, then this is the best method to review all values of the GMSA:
Get-ADServiceAccount -Identity gmsa-pwdexpiry -Properties *
I would not recommend using ADSIEdit to review most GMSA attributes as I find that GUI is limited in showing the correct values for those objects, e.g. this is what happens when you view the ‘principals…’ value using ADSIEdit (called msDS-GroupMSAMembership in ADSI):
Appendix: Why can’t I use an AD group with the switch: PrincipalsAllowedTo..?
Simply: you can! Just a word of warning. I’ve been having intermittent issues in my lab with using AD groups. I decided to base my blog purely on direct computer account memberships directly to the GMSA as I’ve not had an issue with that approach.
If find that the commands: ‘Install-ADServiceAccount’ and ‘Test-ADServiceAccount’ sometimes fails when I use group memberships. Feel free to readily try however, it may due to issues in my lab. In preparing this lab, I could not provide the screen shot of the issues as they’d mysteriously resolved themselves overnight (the worst kind of bug, an intermittent one!)
You can easily run the command to create a GMSA with a security group membership (e.g. ‘pwdexpiry’) as the sole ‘PrincipalsAllowed…’ object:
Then use try running the ‘Install-ADServiceAccount’ and ‘Test-ADServiceAccount’ on the Windows Servers whose computer accounts are members of that group.
Good luck!
Michael

Reset-ADServiceAccountPassword is not valid for gMSA accounts.
https://technet.microsoft.com/en-us/library/hh852255(v=wps.630).aspx
The intermittent issue you were having with groups was due to the server not knowing it was a member of that group. If you reboot the server the Install-ADServiceAccount command would immediately work. Very similar to how a user needs to log off / on to access a share secured by group when just added to that group.
Or just renew the kerberos ticket of the computer :
https://www.normanbauer.com/2016/03/30/how-to-purge-kerberos-tickets-of-the-system-account/