My colleague David Ross has written a previous blog about configuring proxy server settings to allow Azure AD Sync (the previous name of Azure AD Connect) to use a proxy server.
Starting with version 1.1.105.0, Azure AD Connect has completely changed the configuration steps required to allow the Azure AD Connect configuration wizard and Sync. Engine to use a proxy.
I ran into a specific proxy failure scenario that I thought I’d share to provide further help.
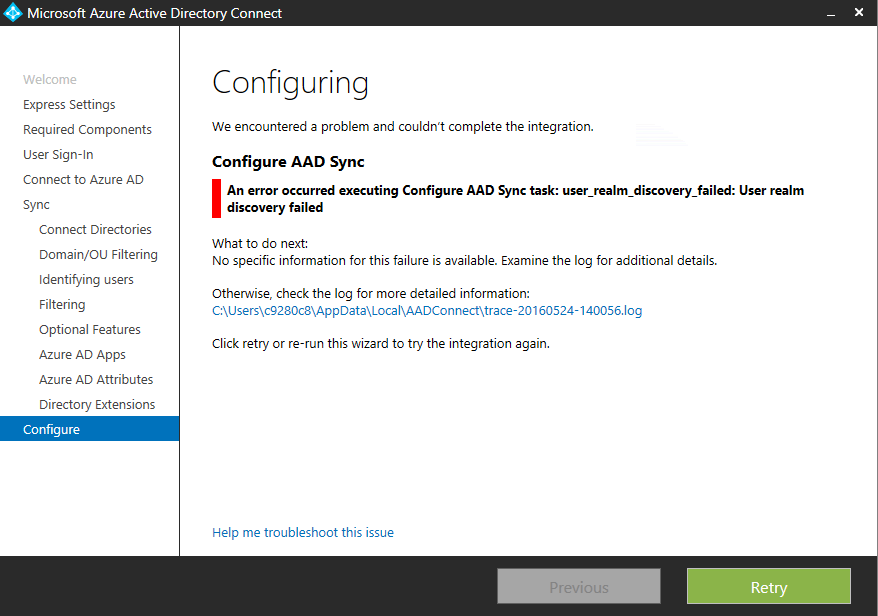
My Azure AD Connect (v.1.1.110.0) installation reached the following failure at the end of the initial installation wizard:
The trace log just stated the following:
Apply Configuration Page: Failed to configure directory extension (True). Details: System.Management.Automation.CmdletInvocationException: user_realm_discovery_failed: User realm discovery failed —> Microsoft.IdentityManagement.PowerShell.ObjectModel.SynchronizationConfigurationValidationException: user_realm_discovery_failed: User realm discovery failed
In this environment, I had the following environmental components:
- The AAD Connect software was going to operate under a service account
- All Internet connectivity was through a proxy server which required authentication
- Windows Server 2012 R2 platform
- Two factor authentication was enabled for O365 Admin accounts
Previously, in order to get authentication working for O365, I set the proxy server settings in Internet Explorer. I tested browsing and it appeared fine. I also had to add the following URLs to the Internet Explorer’s ‘Trusted Sites’ to allow the new forms based authentication (which allowed the second factor to be entered) to work properly with the Azure AD connect wizard:
- https://login.microsoftonline.com
- https://secure.aadcdn.microsoftonline-p.com
So even though my Internet proxy appeared to be working under my admin. account, and Office 365 was authenticating properly during the O365 ‘User Sign-In’ screen, I was still receiving a ‘User Realm Discovery’ error message at the end of the installation.
This is when I turned to online help and I found this Microsoft article on the way Azure AD Connect now handles proxy authentication. It can be found here and is by and large an excellent guide.
Following Microsoft’s guidance, I ran the following proxy connectivity command and verified my proxy server was not blocking my access:
Invoke-WebRequest -Uri https://adminwebservice.microsoftonline.com/ProvisioningService.svc
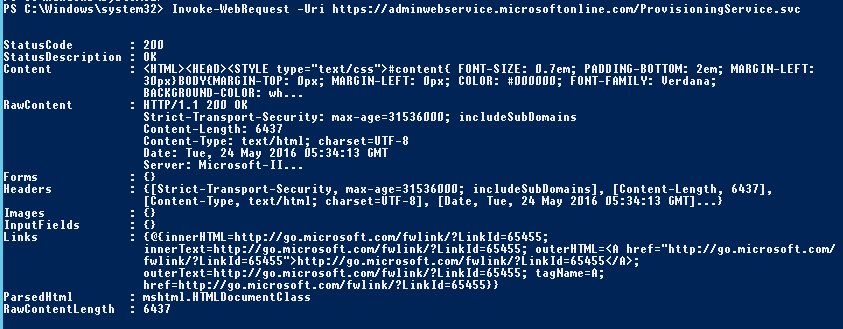
So that appeared to be fine and not causing my issue. Reading further, the guidance in the article had previously stated at the start that my ‘machine.config’ file had to be properly configured. When I re-read that, I wondered aloud “what file?”. Digging deeper into the guidance, I ran into this step.
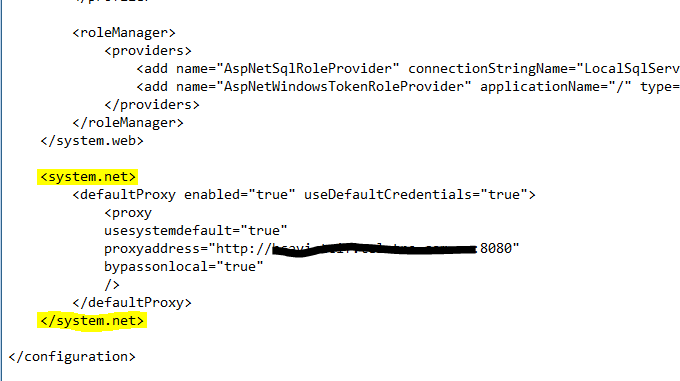
It appears that Azure AD connect now uses Modern Authentication to connect to Office 365 during the final part of the configuration wizard, and that the ‘web.config’ file has to be modified with your proxy server settings for it to complete properly.
Since the environment here requires a proxy which requires authentication, I added the following to the end of the file:
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\Config\machine.config
All new required text are within the ‘<system.net>‘ flags. NOTE: The guidance from Microsoft states that the new code has to be ‘at the end of the file’, but be sure to place it BEFORE the text: ‘</configuration>’:
I saved the file, and then clicked ‘Retry’ button on my original ‘user realm discovery failure’ message (thankfully not having to attempt a completely new install of Azure AD connect) and the problem was resolved.
Hope this helps!

This works fine, when I am logged into the DC running AAD Connect. However if I am not logged in the AAD Connect does not run until I once again login to the DC. Any ideas for this?
-Callahan-
make sure you are have the Microsoft Azure AD services running as a service account which has outbound proxy access.
Thank you Michael for posting this one…. Saved me a lot of time.
Oh boy, this did save me a lot of headache..however, im only half way there! I entered all the required info, i actually manage to finish the AD connect wizard and got this on the last page: AD connect was successfully configured, password sync cannot be configured. Check event log for more info.
Going there, i can see some information events (no errors) saying that the sync failed to resolve the name ‘login.windows.net’
I tried browsing to it – it’s working (this is part of the URL list that the network admin has already whitelisted on the web proxy)
I then went to powershell: import-module AdSync
Start-AdSyncSyncCicle -policyType initial
Received a big big error saying that “user realm discovery failed—>System.Net.WebException: The remote name could not be resolved: ‘login.windows.net’
My understanding is that the sync is trying to access that fqdn through 443 and is not going through the proxy server.
Any ideas?
Hello, we have the same error on our side. After lot of searches, we found nothing… Did you get through this ?
Hello,
have you ever solved that Problem? We have the same error:
The remote name could not be resolved: ‘login.windows.net’
Thanks for the guide legend! This was my last ditch attempt to get the sync working again. Terrific!