Recently I was asked to implement an Office 365 Preview for Enterprises tenant that would demonstrate the new functionality provided by Windows Azure Active Directory Rights Management (AADRM). Windows Azure Active Directory is the cloud identity management service that underpins Office 365 and many other Microsoft cloud products; you can read more about it here.
Rights Management Services (RMS) are a feature set that allows for the protection of information, regardless of where it goes or who it is sent to. When the content owner enables RMS on a file or an email, the owner specifies what other users can actually do with the content – be it view, read, copy, forward or print. While there’s nothing to stop the recipient taking a screenshot of the information, a photo of the screen or even just writing it down, it does reduce the options available for redistributing confidential / sensitive material.
SharePoint Online and Exchange Online can be enabled for RMS with Office 365 Enterprise / Education Plans 3 and 4 , however it is not enabled by default.
Activating Windows Azure Active Directory Rights Management
AADRM can be activated via the Admin Portal or using PowerShell, both requiring an active Office 365 Preview for Enterprises tenant.
Method 1 – Admin Portal
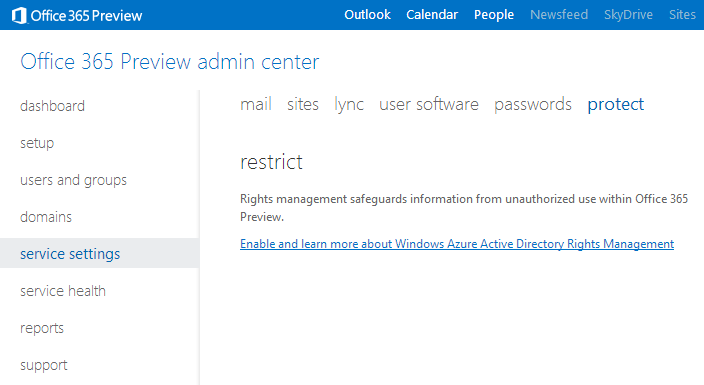
Through the Office 365 Preview admin centre, browse to service settings then to protect
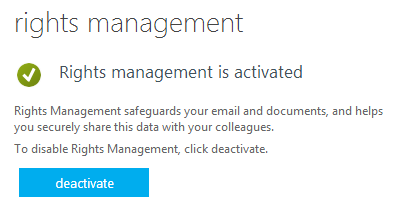
Click on the link to Enable and learn more about Windows Azure Active Directory Rights Management where a confirmation page should appear to show that RMS has been successfully activated.
Method 2 – PowerShell
Microsoft have released a new Windows Azure AD Rights Management administration module which can be downloaded from here. Once the WindowsAzureADRightsManagementAdministration.exe has been installed:
- Open Windows PowerShell
- Connect to the AADRM service and enter Office 365 credentials when prompted
Import-Module AADRM
Connect-AadrmService –Verbose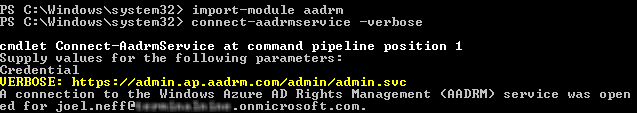
- Enter Office 365 Preview administrator credentials
-
To enable AADRM, type the following commands:
Enable-Aadrm
Disconnect-AadrmService
Rights Management for Exchange Online Preview
IRM provides the functionality to apply persistent information protection to email messages and any attachments contained within them. Through Outlook and OWA, users are able to control the rights that the recipients of an email have over the contents contained within the message. Recipients can be restricted from performing certain actions such as:
- Forwarding emails or attachments to other parties
- Printing of emails or attachments
- Copying and pasting content from emails or attachments
Configure IRM for Exchange Online Preview
-
Connect to Exchange Online PowerShell
$cred = Get-Credential
$session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri https://ps.outlook.com/powershell/ -Credential $cred -Authentication Basic –AllowRedirection
Import-PSSession $session -
Enable IRM for Exchange Online
Enable-OrganizationCustomization
Set-IRMConfiguration –RMSOnlineKeySharingLocation https://sp-rms.ap.aadrm.com/TenantManagement/ServicePartner.svc
Import-RMSTrustedPublishingDomain -RMSOnline -name “RMS Online”
Set-IRMConfiguration -InternalLicensingEnabled $true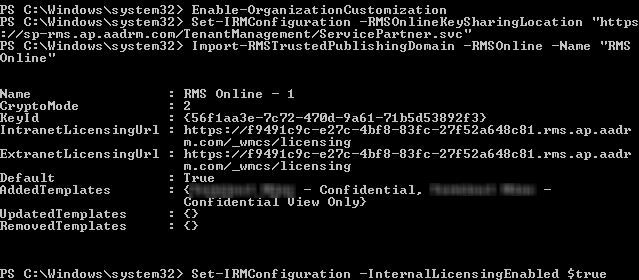
-
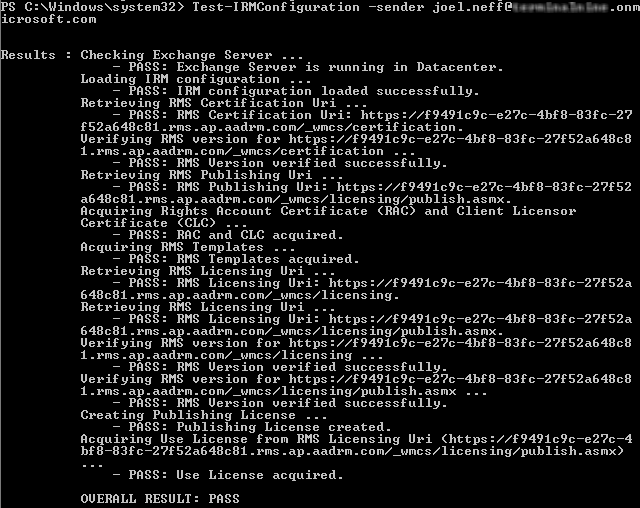
The configuration can be tested with the following command:
Test-IRMConfiguration –sender user@companyname.onmicrosoft.com
Note: When executing the Set-IRMConfiguration command, I have used the RMS Key Sharing Location for the Asia Pacific region. If the tenant is located in another datacentre, ie Europe or North America, modify the URL to sp-rms.eu.aadrm.com or sp-rms.na.aadrm.com respectively.
Enable Information Rights Management for SharePoint Online
Information Rights Management is activated within the Office 365 Portal.
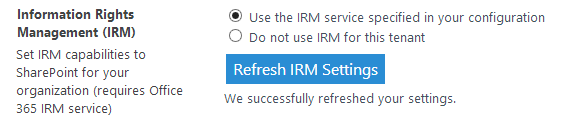
Within the SharePoint admin center, browse to settings
Under Information Rights Management (IRM), select the Use the IRM service specified in your configuration radio button and click Refresh IRM Settings. It should display the message “We successfully refreshed your settings.”
Configure SharePoint Online for Rights Management
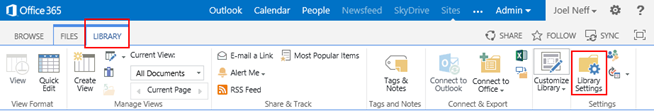
- Logged in as an administrator, open an existing SharePoint Online site or create a new one
-
Browse to Documents then the Library tab and then Library Settings
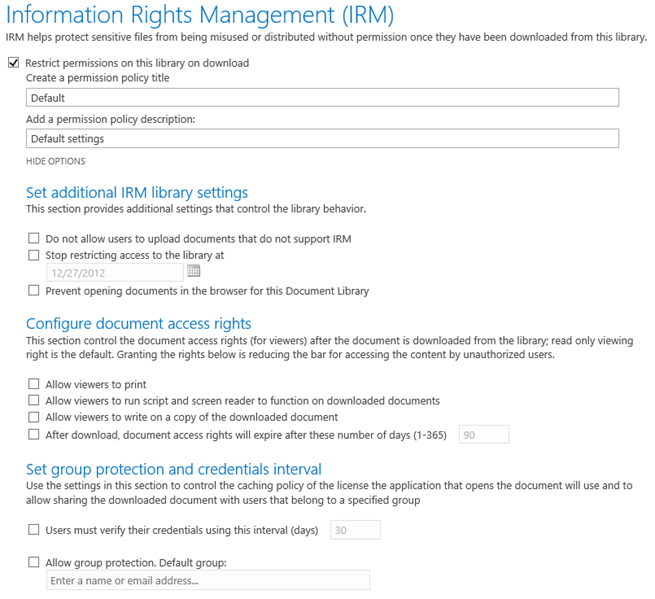
- Under Permissions and Management select Information Rights Management
-
Click Restrict permissions on this library on download, name the policy and set any additional policy options as required
Enable Office 2013 for AADRM
Office 2013 supports AADRM, however it is not enabled by default. Any PC that will be used for IRM will need to have the following registry key added, either manually or distributed via Group Policy
Under HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\15.0\Common\DRM, create a new REG_DWORD named UseRMSOnline with the value set to 1

Excellent Post – thanks!
Thanks – Saved me a lot of research time.