Yesterday, the Active Directory team announced the Developer Preview of Windows Azure Active Directory (AD). Windows Azure AD is Identity Management as a Service. Today, it is the identity provider for Office 365, Dynamics CRM Online, and Windows Intune. The Developer Preview enables developers to implement Web Single Sign-On (SSO) for Software as a Service, and line-of-business, and cloud applications.
With the new announcement, Vittorio Bertocci published a deep-dive article that describes Web SSO with Windows Azure AD. A how-to guide, which walks developers through implementing Web SSO with ASP.NET, was also published to the Windows Azure website.
However, the how-to guide only discusses implementing Web SSO with ASP.NET 4. This post walks you through what is required to implement it with ASP.NET 4.5.
Implementing Web SSO with ASP.NET 4.5
With Visual Studio 2012 and .NET Framework 4.5, building claims-aware applications has changed.
Firstly, the Visual Studio tools (such as Add STS Reference…) and the command-line tool, FedUtil.exe, that have been packaged in the Windows Identity Foundation (WIF) SDK are no longer be shipped. Instead, you install a new Visual Studio extension, Identity and Access Tool. Secondly, the claims-related classes that have also been packaged in the WIF SDK are a first-class citizen of the core framework. In fact, many of these classes (such as the Claim class) are packaged in the mscorlib assembly!
All of this means that how you configure an ASP.NET Web Forms or MVC application for federation with a remote Security Token Service (STS)—in the context of this post, this STS is Windows Azure AD—is different.
If you are walking yourself through the how-to-guide that I described earlier, you must configure Fabrikam’s ASP.NET MVC application for federation with Windows Azure AD (see Step 3 – Protect the ASP.NET application via WS-Federation and onboard the first customer in this guide) as follows:
1. In Visual Studio, right-click the ASP.NET MVC Web Application project in Solution Explorer and select Identity and Access….
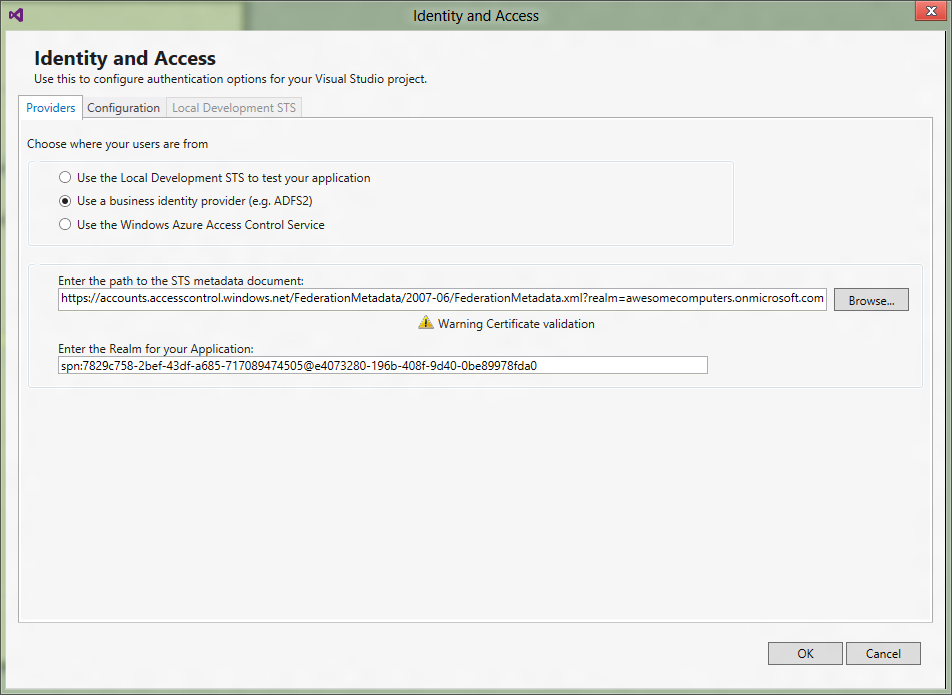
2. In the Providers tab of the Identity and Access window:
- Select Use a business identity provider
- Enter the following URL into Enter the path to the STS metadata document, where <realm> is the domain name of your Office 365 tenancy:
https://accounts.accesscontrol.windows.net/FederationMetadata/2007-06/FederationMetadata.xml?realm=<realm> - Enter the Audience URI that is created by Step 2- Provision the ASP.NET MVC application in Windows Azure Active Directory in the guide into Enter the Realm for your Application; for example:
spn:7829c758-2bef-43df-a685-717089474505@e4073280-196b-408f-9d40-0be89978fda0
3. Click OK.
The following figure shows the completed Identity and Access window.
4. In the ASP.NET MVC Web Application project, open the Web.config file.
5. In the Web.config file, add the certificateValidation element to the system.identityModel/identityConfiguration element as follows:
<certificateValidation certificateValidationMode="None" />
The following snippet shows the completed Web.config file.
<system.identityModel>
<identityConfiguration>
<audienceUris>
<add value="spn:7829c758-2bef-43df-a685-717089474505@e4073280-196b-408f-9d40-0be89978fda0" />
</audienceUris>
<issuerNameRegistry type="System.IdentityModel.Tokens.ConfigurationBasedIssuerNameRegistry, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089">
<trustedIssuers>
<add thumbprint="3464C5BDD2BE7F2B6112E2F08E9C0024E33D9FE0" name="spn:00000001-0000-0000-c000-000000000000@495c4a5e-38b7-49b9-a90f-4c0050b2d7f7" />
</trustedIssuers>
</issuerNameRegistry>
</identityConfiguration>
</system.identityModel>
<system.identityModel.services>
<federationConfiguration>
<cookieHandler requireSsl="false" />
<wsFederation passiveRedirectEnabled="true" issuer="https://accounts.accesscontrol.windows.net/v2/wsfederation" realm="spn:7829c758-2bef-43df-a685-717089474505@e4073280-196b-408f-9d40-0be89978fda0" reply="https://localhost/OrgIdFederationSample" requireHttps="false" />
</federationConfiguration>
</system.identityModel.services>
6. Complete steps 7—12 of Step 3 – Protect the ASP.NET application via WS-Federation and onboard the first customer in the guide.
When you run the ASP.NET MVC Web application project, you will be redirected to the Office 365 identity provider page, where you can log yourself in using your Office 365 credential!

Thanks Chris,
Very useful post. Still coming to grips with framework 4.5 myself. Much to learn.
-mark
Hi, Good pointers, but I’m seeing “there is no valid metadata document….” as an error on the first wizard text box. I’m probably doing something stupid, but what?
I get the same error. What is the correct URL for the “STS Metadata document”?
Hi Rake,
Taking into account both the adjustment to the URL format from a while ago, and the change in the actual URL from more recently, you need:
https://login.windows.net//federationmetadata/2007-06/federationmetadata.xml
Cheers,
Nick
Oops, the posting process fouled up the URL. Here it is with some extra spaces to try and clarify:
https: // login . windows . net / Tenant Name Here / federationmetadata / 2007-06 / federationmetadata.xml
Thanks, much appreciated.