A RACF Management Agent for Microsoft Identity Manager ? Isn’t there one in the box? No. Host Integration Management Agents were deprecated when Microsoft released Forefront Identity Manager as the successor to Identity Lifecycle Manager (ILM). I understand it was partly due to lack of demand for the integration, and the reliance on Host Integration Server (HIS) along with the move in operating system support 32-bit (in ILM) to 64-bit (in FIM). With ILM integration with Host Systems via HIS you were required to map out the key sequences anyway.
But it’s 2019 and ILM was released in 2007 and FIM in 2010. Why are you posting about a RACF Management Agent? A rudimentary use case would be;
- RACF still exists in environments and you just need to have visibility of which users have accounts
- you can then base notifications or other events off this information during lifecycle management
- you may want to implement password sync to RACF
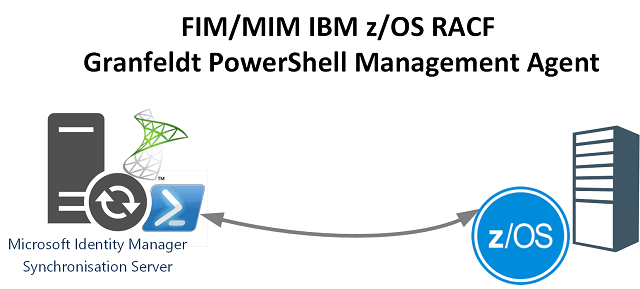
Integrating Microsoft Identity Manager with RACF
I’m not going to promote this integration as gold-standard or even best practice. With the preface above and the title even stating “rudimentary” here is a solution that also fits the title of my blog site “Bespoke Identity and Access Management Solutions“.
Disclaimers now aside, my Rudimentary Microsoft Identity Manager Management Agent for RACF;
- leverages the Granfeldt PowerShell Management Agent
- leverages the x3270 Client and automation using PowerShell as detailed in this post
If you haven’t used the Granfeldt PowerShell Management Agent before then start here. This post will only detail the Schema and Import Scripts to get you visibility of users in RACF and allow a Join to a Metaverse Hologram. The process to do that can be expanded on if you wanted to implement exports to RACF (e.g. for Account Disablement, Account Creation or Deletion) or Password Sync.
RACF PowerShell Management Agent Schema Script
The schema script below sets up an Object Class for the MA named racfUser with a single attribute named racfID which is the UserID from RACF. You can rename it if required.
RACF PowerShell Management Agent Import Script
The Import Script below uses the x3270 Client as detailed in this post and PowerShell to orchestrate it. It issues the SEARCH CLASS (USER) command to list all accounts, then parse the x3270 Tracefile to extract them. This is a rudimentary method (that works) but you may want to run a job on the RACF Host and then transfer a file out also using the x3270 HTTPD method and process it that way. Up to you.
The script functionality provides Paged Imports. That needs to be enabled on the PowerShell Management Agent. The script then uses the Run Profile Page Size to process the users through the MA. Username and Password for the account used to connect to RACF are passed from the PowerShell MA configuration. Only Full Sync is supported, no Delta Sync’s here.
Summary
If you made it this far, oh dear. But hopefully it has given you hope of an approach that can be used to get a rudimentary level of integration of RACF with Microsoft Identity Manager quickly. And good luck.
