Q: Can multiple Office 365 tenants use a single AD FS instance to provide SSO?
A: Yes
Overview
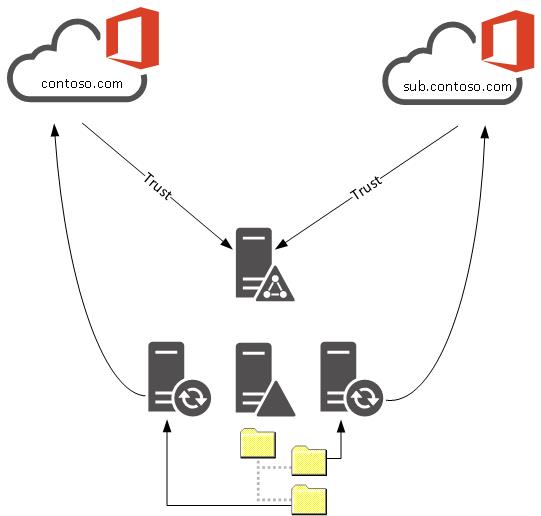
- Office 365 tenant 1 is configured with the domain contoso.com
- Office 365 tenant 2 is configured with the domain sub.contoso.com
- Single Active Directory Forest with multiple UPNs configured (contoso.com and sub.contoso.com)
- Single AD FS instance including an AD FS Proxy/Web Application Proxy published with the name sts.contoso.com
- Two instances of Azure ADConnect configured with container filtering to ensure users are only synchronised to a single tenant
Configuring SSO
The Federation Trust for Tenant 1 is configured by establishing a Remote PowerShell session (with the Azure Active Directory Module loaded) and running the standard ‘Convert-MsolDomainToFederated’ cmdlet:
[code]Convert-MsolDomainToFederated -DomainName contoso.com -SupportMultipleDomain[/code]
When it comes to configuring Tenant 2, things become a little more tricky. One of the features of the ‘Convert-MsolDomainToFederated’ cmdlet is that it performs the required configuration on Office 365 as well as the AD FS Farm. If you attempt to run this cmdlet against an AD FS Farm that has a Federation Trust established with a different tenant, it will fail and return an error. Therefore, we need to make use of the ‘Set-MsolDomainAuthentication’ cmdlet which only makes configuration changes to Office 365 and is usually used for establishing Federation Trusts with third party IdPs.
The first step is to export the token-signing certificate from the AD FS farm either via Windows Certificate Manager or via PowerShell:
[code]$certRefs=Get-AdfsCertificate -CertificateType Token-Signing
$certBytes=$certRefs[0].Certificate.Export([System.Security.Cryptography.X509Certificates.X509ContentType]::Cert)
[System.IO.File]::WriteAllBytes("c:\temp\tokensigning.cer", $certBytes)[/code]
Next, establish a Remote PowerShell session with Tenant 2 and then run the following script to configure the trust:
[code]$cert = New-Object System.Security.Cryptography.X509Certificates.X509Certificate2("C:\temp\tokensigning.cer")
$certData = [system.convert]::tobase64string($cert.rawdata)
$dom="sub.contoso.com"
$url="https://sts.contoso.com/adfs/ls/"
$uri="http://sub.contoso.com/adfs/services/trust/"
$ura="https://sts.contoso.com/adfs/services/trust/2005/usernamemixed"
$logouturl="https://sts.contoso.com/adfs/ls/"
$metadata="https://sts.contoso.com/adfs/services/trust/mex"
#command to enable SSO
Set-MsolDomainAuthentication -DomainName $dom -Authentication Federated -ActiveLogOnUri $ura -PassiveLogOnUri $url -MetadataExchangeUri $metadata -SigningCertificate $certData -IssuerUri $uri -LogOffUri $logouturl -PreferredAuthenticationProtocol WsFed[/code]
Once configured, the configuration of both tenants can be validated using the ‘Get-MsolDomainFederationSettings’ cmdlet. The only difference when comparing the tenant configuration should be the ‘FederationBrandName’ and the ‘IssuerUri’ values.

Great post, thank you for documenting this scenario.
Good post! But this would still imply that one user can only authenticate to one tenant – because they would only have one UPN – correct?
That’s correct.
David, is this a supported scenario by Microsoft?
I’m not aware of an official support stance from Microsoft on this pattern.
Great information.
Could a single tentant use multiple AD FS instances for authentication?
e.g. domain1.com uses ADFS farm sts.domain1.com
and
domain2.com uses ADFS farm sts.domain2.com
domain1.com and domain2.com are part of the same tentant.
Thanks.
Hi Thomas,
I haven’t tried this but I believe it will work. The only caveat being you that wouldn’t be able split sub-domains across multiple AD FS instances. Let us know how you go!
Excellent post. Helped me a lot
Has anyone tried this with two different Proxy servers as well? our situation is unique in that we’d want to brand the proxy login page (and differnet language) according to which of the domains/upns are logging on.. Would that be possible?
Hi Matt, this won’t be possible with two different proxy servers as you require a single AD FS namespace.
It may be possible to code AD FS to present different style pages based on the URL referral from Office 365 but this is not something I have tried. If you go down this path and are successful I would love to hear about the results.
HI David,
is this possible when we have 2 different account i.e. Exchange Online plan 2 & Office 365 E3?
Hey Kalpesh, yes, you can have mixed license environment in your tenant. Some users can have a EP2 license and others an E3.
Also fyi-
I don’t know what you would do this, but, you can have an E3 with EXO unticked, and an EP2 for the same user. Odd one, but, I hope I haven’t confused you!?!
Cheers,
Lucian
Hi all,
I have a question.
In my organization we have a on-prem Exchange 2010 with about 30 customers (one single forest with about 30 UPN Suffix added).
We need to move to Office 365, and every customer have is own tenant.
This solutions is the best? I have to create about 30 servers with Azure AD Connect.
But I only need one AD FS Proxy/Web Application Proxy, correct?
Thanks