Hi all – this blog will cover off some information to assist with multilingual/international deployment of Azure MFA server. There are some nuances of the product that make ongoing management of language preferences a little challenging. Also some MFA Methods are preferable to others in international scenarios due to carrier variances.
Language Preferences
Ideally when a user is on-boarded, their language preferences for the various MFA Methods should be configured to their native language. This can easily be achieved using MFA Server, however there are some things to know:
- Language settings are defined in in Synchronisation Items.
- Synchronisation Items can be set in a hierarchy so that settings in the most precedent Synchronisation Item apply.
- Language settings set explicitly in Synchronisation Items apply at FIRST SYNC ONLY. Adding, removing or changing Sync Items with explicitly set language configurations will have no effect on existing MFA Server users.
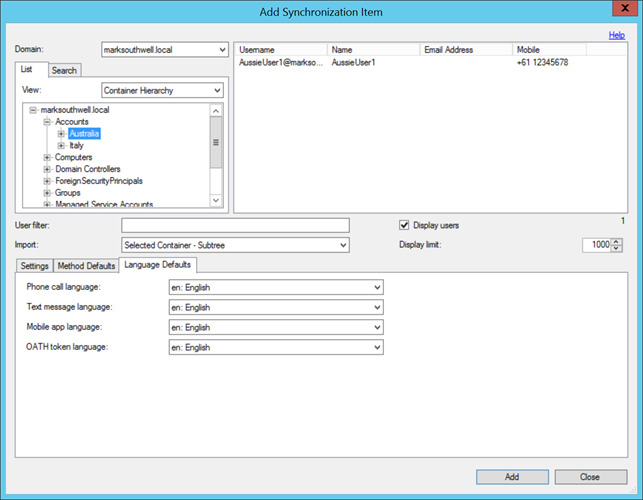
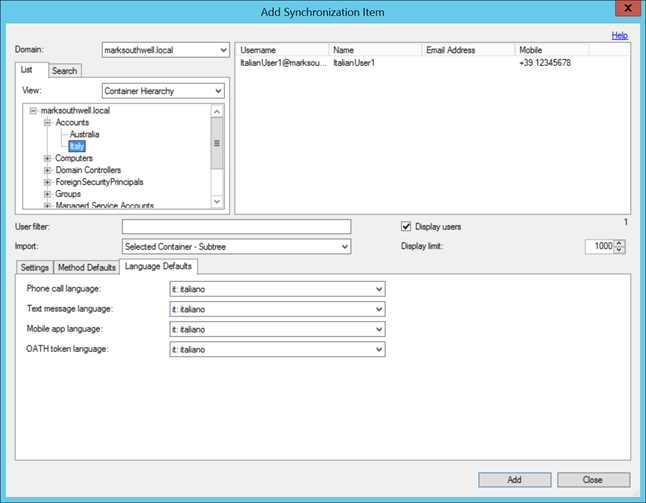
I’ll cover off how to get around item 3 a bit later with non-explicitly configured language settings. To demonstrate hierarchical application of Sync items – first create two Sync Items with different explicitly set language settings as below. I’ve used Active directory OUs to differentiate user locations, however AD security groups can be used too, as can an LDAP filter:
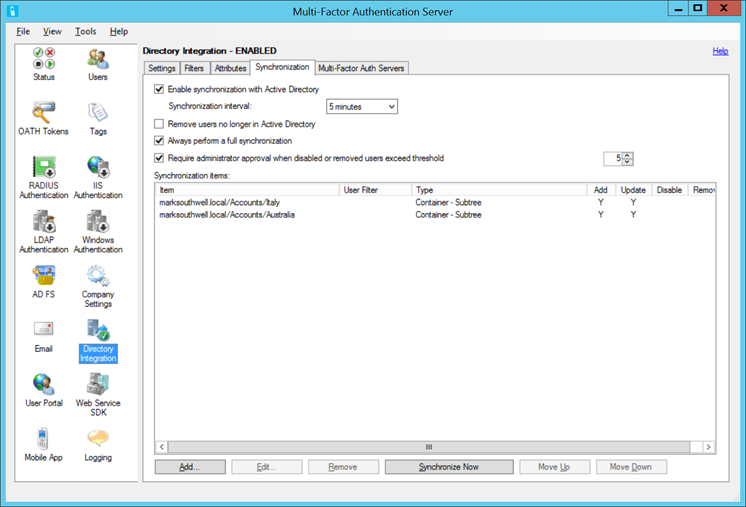
Then set them in the required hierarchy, in this case our default language is English for the Aussies, then we have an overriding Sync Item for the Italians – easy:
The above is all well and good if you are 100% guaranteed that users will be in the correct OU, group, or have the user filter apply when MFA server synchronises. If they are subsequently modified and a different Sync Item now applies, their language settings will not be updated. I’ll now cover how to get around this next.
Use of Language Attributes to control Language Settings
MFA Server has the option to specify a language attribute in user accounts to contain the short code (e.g. en = English) for language preferences. When the account is imported, the user’s default language can be set based on this attribute. Also unlike explicitly configured language settings, when a Sync Item is configured to use language attributes it will update existing users if the language short code in their account changes.
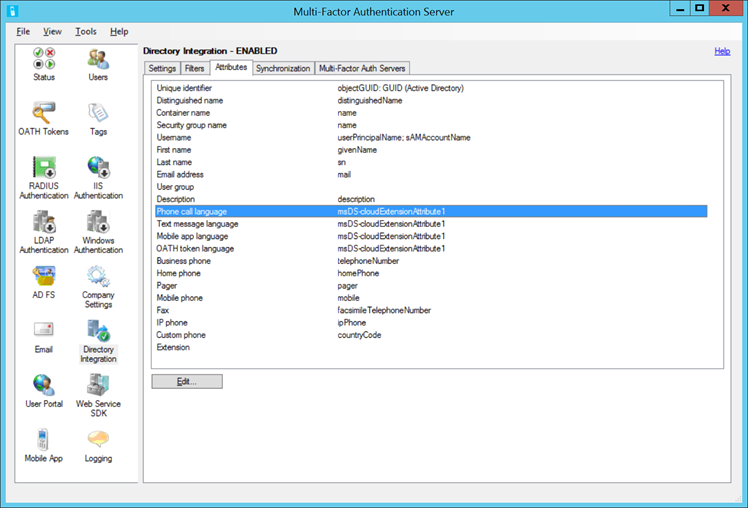
To use this feature, first define an AD attribute that stores the language short code within the Attributes tab in the Directory Integration. Shown below I’m using an AD Extension attribute to store this code:
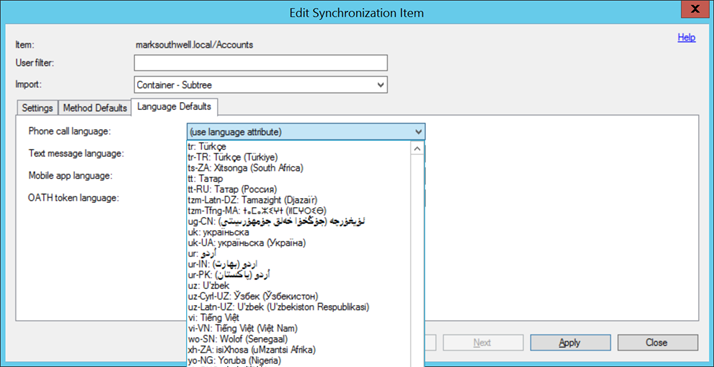
Then create a Sync Item that covers all your users, and configure “(use language attribute)” instead of explicitly setting a language – it’s the last item on the list of languages so unless you’re Zulu it’s easy to miss. By the way, those are the short codes for the language attribute for each language listed in this drop down list. Once user accounts have been configured with the language short code in the specified attribute, on next sync their language will be updated.
Other Stuff to Keep in Mind
When dealing with international phone carriers, not all are created equal. Unfortunately, Microsoft has little control over what happens to messages once they’re sent from Azure MFA Services. Some issues that have been experienced:
- Carriers not accepting two way SMS, thus MFA requests time out as user One Time Password responses are not processed.
- Carriers not accepting the keypad response for Phone call MFA, again resulting in MFA request time out.
- Carriers spamming users immediately after SMS MFA has been sent to users.
- Users being charged international SMS rates for two-way SMS (makes sense, but often forgotten).
In my experience SMS has proven to be the least reliable, unless the Mobile MFA App/OATH can be used Phone is the better method for International users.
Often overlooked is the ability to export and import user settings using the MFA Server Console. You can export by selecting File/Export within the console. The CSV can then be updated and re-imported – this will modify existing user accounts including MFA Method preference and language defaults.
One Last Thing
For Apple iPhone users, Notifications must be enabled for the MFA Mobile App as the App will fail to activate with a timeout error if Notifications are disabled. Notifications can be enabled in iOS via navigating to Settings/Notifications/Mulit-Factor and enabling “Allow Notifications”. Changing this setting can take a little while to apply, so if the Mobile App still does’t activate after enabling Notifications, wait a bit then try again.

Hi Guys,
I know this blog post is a little old, so hopefully you will reply! I’ve set up MFA using two way text messages (client has requested this rather than the app for reasons of their own). In my testing I’d say about 90% of the time I get the text message from a +61 number (I’m in Australia) and replying is fine.
However the other 10% of the time I get a message from a +1xxx number and since not everyone can reply to international text messages, they need to wait until the process times out before trying again and hoping for an Australian message.
Is there any way that I can ensure that the authentication text messages ONLY come from local sources?
Thanks very much!
Hello Mark, Really nice article. You an mentioned the import/ export using csv file option. Can the import option be used to change the current MFA method selected by the user? For example, if the user has chosen sms, can we change the method to use phone call using import?
2) Also, is import a bulk option all the time? can we use import to make changes to only handful of users?