Every once in a while I come across a problem which is vexing and irritating and equally, an absolute joy when it is finally resolved.
The Scene
This particular issue had been on-going for some time with one of my customers with reports coming in from various people saying that they were being prompted to authenticate when opening an Office document in SharePoint Online. “I’ve already logged in so why do I keep getting these prompts?!” – It’s a fair question, especially since the organisation had implemented AD FS to reduce the frequency of authentication dialogue boxes. It seemed that Microsoft was not only being overprotective but overbearing as well. Here’s the dialogue I’m talking about by the way:
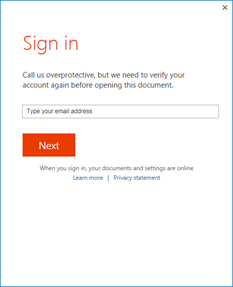
Figure 1 – Overprotective
Along with this issue, the customer had started to map network drives to SharePoint. Let’s face it, it’s easier to manage files in a folder structure than in the SPO web interface, and with improvements over the last few years with SharePoint mapping network drives actually works, or at least is should work. While it was working some of the time, there were reports of access issues to these mapped drives, and a different dialogue box which while uglier, on first glance appeared more promising from a technical perspective. A recommendation for a fix and a reference to a KB article!
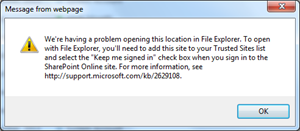
Figure 2 – Ugly but useful
There are a plethora of articles, wikis, forum posts, etc out there which all talk about adding your SharePoint Online sites to your browser’s Trusted Sites list. The referenced KB article covers it off nicely, and I’ve added the link in case you’ve not come across it, here.
In my particular case the SharePoint Online domains were all happily existing in the IE Trusted Sites list (I checked about 30 times during my investigations)
I’ve mentioned that AD FS is in play, further a redirection URL http://Intranet.KloudySky.com.au is used with a Smart Link in this particular environment to provide a more seamless login experience. Until very recently you were not able to customise the Office 365 Portal page, https://login.microsoftonline.com. Check out this article for more info on how to brand the Sign-In Page with company branding.
While you can now brand the Sign-In page to your heart’s content (if you have an Azure subscription along with your O365 subscription), you’ll need to type in your UPN at least once (normally not an experience IT wants to establish for a new Intranet rollout), and so smart links are not yet dead.
There’s a couple of good resources for creating SmartLinks, including one written by a Kloudy here and a good Office365 community article here which discusses some of the components of the link.
The Solution
I’ve set the scene, and for most of you you’ve probably bypassed everything above and come straight to this point. For those of you who took the slow route of reading from the top; Thanks for sticking around!
The problem I was seeing was due to a very simple issue really. You need to check the check box which says “Keep me signed in”. It even says so in the ugly helpful dialogue box above. The thing is, if you’re using AD FS and SmartLinks you don’t actually hit the Office 365 login page and so don’t get the opportunity to sign in. We need to pass the “Keep me signed in” option to the AD FS server somehow, and the only way to do that is to encode it in the URL.
How do we do that? As it turns out there’s a way!
At the end of the SmartLink is the LoginOptions attribute.
LoginOption=3 will pass the “Keep me signed in” option as off (Not checked)
LoginOption=1 will pass the “Keep me signed in” option as on (Checked)
Don’t keep me signed in. Boo!!!
https://myadfs.Kloudysky.com.au/adfs/ls/?wa=wsignin1.0&wtrealm=urn:federation:MicrosoftOnline&wctx=[wctxValue]%26wreply%3Dhttps%253A%252F%252FKloudySky%252Esharepoint%252Ecom%252F%255Fforms%252Fdefault%252Easpx%26lc%3D1033%26id%3D123456%26%26LoginOptions%3D3
Keep me signed in. Yay!!!
https://myadfs.Kloudysky.com.au/adfs/ls/?wa=wsignin1.0&wtrealm=urn:federation:MicrosoftOnline&wctx=[wctxValue]%26wreply%3Dhttps%253A%252F%252FKloudySky%252Esharepoint%252Ecom%252F%255Fforms%252Fdefault%252Easpx%26lc%3D1033%26id%3D123456%26%26LoginOptions%3D1
I only made this change on the Internal SmartLinks by the way. I’ve left the SmartLinks published to the Internet with LoginOptions=3, we don’t really want people on untrusted PCs and devices to remain logged into Office 365 services.
I’d like to make a big thankyou to Carolyn at Microsoft PSS for helping me resolve this issue.

Hi Jason,
Thanks for this article. I have been trying to find a solution to this problem and stumbled upon this link.
Where exactly on the AD FS servers can I make this change to allow me to modify the SMART LINK URL?
How do I bulk modify the LoginOption for all users so if they are coming through AD FS then they do not have to retype thier passwords again and again?
Hi Junaid,
The smartlink is a redirection URL which you need to add to a web server within your organisation (such as an IIS server). Specifically, if you create a new website for mySharePoint..com and add a redirect to the smart link.
When a user clicks on this new link to access SharePoint, it will tell ADFS to set the login option.
Thanks,
Jason
https://login.microsoftonline.com/login.srf?wa=wsignin1.0&whr=adfs.XXXXXXX&wreply=https://crdistrict-my.sharepoint.com&LoginOptions=1
Worked for us till yesterday. Did MS change something
We’re getting the same problem also. Our SmartLink was working until 2 weeks ago. We are getting prompts again when opening office documents from SharePoint Online. Anybody knows what’s going on?
Hey Guys,
I’m not aware of any changes which would effect this. Though I’ll have a look. In the mean time have a walk through the following article to see if you can come to a resolution: https://support.microsoft.com/en-us/kb/2535227