Microsoft Forefront TMG (Threat Management Gateway) has been the primary way Lync Web Services have been published in the past. With the untimely demise of TMG, the only Microsoft product (other than IIS) with reverse proxy functionality is Microsoft Forefront UAG (Unified Access Gateway). TMG will continue to be supported until 2015 for mainstream support and 2020 for extended support. If TMG is not already installed however, technically it cannot be used for a new installation.
In this blog I will explain how to setup UAG 2010 Service Pack 3 to publish all Lync 2013 reverse proxy features including mobility (for Lync mobile clients) and Office Web Apps. But first a little background unless you want to jump straight to UAG 2010 Configuration.
IIS ARR (Application Request Routing)
According to this NextHop blog Using IIS ARR as a Reverse Proxy for Lync Server 2013, IIS ARR is the only supported Microsoft solution for customers who do not already own TMG. A couple of things to note is that IIS ARR cannot do pre-authentication (not supported for Lync anyway) and there does not seem to be any sizing or scaling documentation out yet.
So IIS ARR looks like a solution if you just publish Lync, or if pre-authentication is not important to you – and this seems to be the way most Microsoft products like Exchange and SharePoint are going.
A recent customer engagement had a requirement for pre-authentication and authorisation (allowing only members of a specific group access to Outlook Web App for example) for Exchange 2010, SharePoint 2013 and FIM 2010. Additionally Lync 2013 required no pre-authentication or authorisation. TMG had been planned for and following the end of life statement above, UAG 2010 was chosen. IIS ARR did not meet all of the requirements.
UAG 2010 – No Official Support For Lync
It is important to note up front that Lync 2013 is not officially supported on UAG 2010. UAG 2010 Service Pack 3 provided support for publishing Exchange 2013 and SharePoint 2013, but Lync was noticeably absent. Additionally, Office Web Apps Server 2013 is not specified as supported.
What’s new in Forefront UAG Service Pack 1 Update 1 added support for publishing Lync 2010 Lync Web App (and SharePoint 2010 Office Web Apps) and lists some known issues including ‘Forefront UAG does not support Lync Mobility scenarios’. More information at Publishing Lync web services
Ben Ari from the Microsoft UAG CSS team (who publicly seems to know more about UAG than anybody else) wrote a clarification blog UAG Lync Mobility and other Lync clients stating:
“UAG does not support accessing Lync using Lync Mobility on any platform, nor the use of the Lync software client. The only thing that IS supported is using the Web-based version of the Lync client. For customers who need to publish Lync for Mobility and the software client, Microsoft recommends publishing the Lync Edge server using TMG, or a comparable transparent-publishing firewall solution (note, though, that using the TMG server that’s on your UAG server is not supported for this purpose)”
At that time, Lync 2013 had reached RTM but not General Availability so I assume this references Lync 2010. Even the official TechNet article on Lync 2013 Reverse Proxy configuration only lists TMG and ISA as the Microsoft options.
Investigating using UAG 2010 to Publish Lync 2013
Bearing in mind the lack of support from Microsoft, our project decided to try using UAG to publish all Lync 2013 web services including mobility and Office Web Apps and see how far we got. Looking into publishing Lync on UAG 2010 I found three main articles which pointed me in the right direction:
Publish Lync 2010 with ForeFront Unified Access Gateway 2010 (UAG)
The blogs above cover a lot of the steps required for Lync Web App and mobility, but the full list of reverse proxy functions we required were:
- Meeting join
- Dialin page
- Lync Web App
- Lync 2013 and Lync 2010 mobile clients
- Lync Windows Store App (Lync MX)
- Lync autodiscover
- Persistent Chat administration
- Lync client Address book web search
- Lync client Address book group expansion
- Office Web Apps upload and presentation from Lync client and Lync Web App
UAG 2010 Configuration
I won’t cover UAG initial configuration and certificates here, except to say that you need a UC Certificate from a public certificate authority with SAN names containing the FQDNs of:
- Lync trunk public host name
- Lync External Web Services
- Lync Meet Simple URL
- Lync Dialin Simple URL
- Lyncdiscover for each SIP domain
- Office Web Apps farm external URL
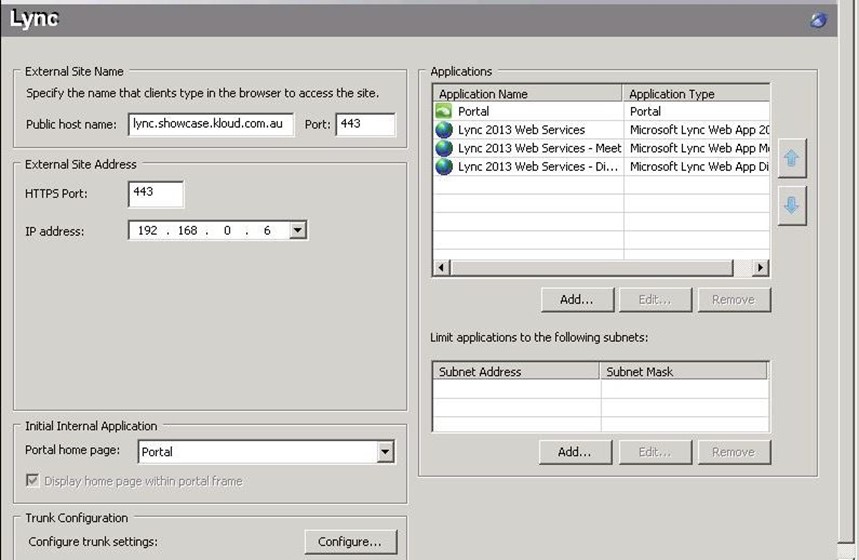
Create Trunk
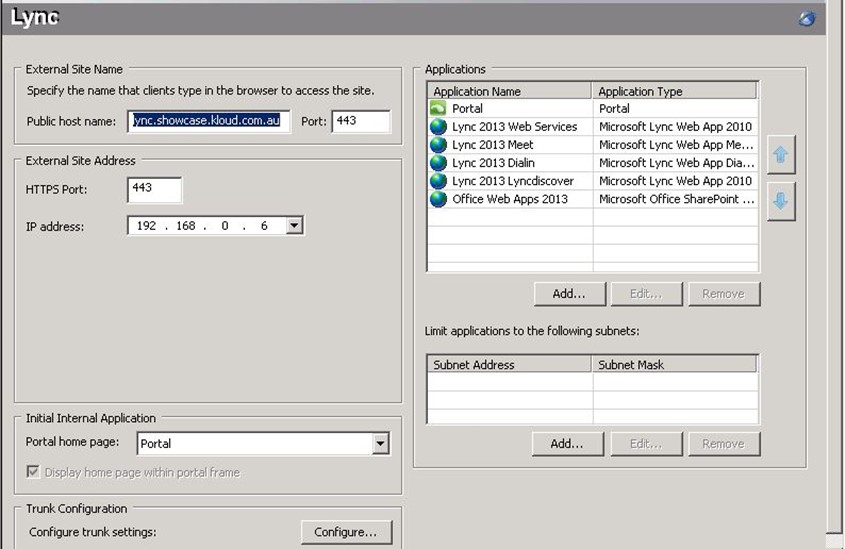
The first step to publish Lync with UAG 2010 is to create a new trunk. This has to be a separate trunk to the one used for Exchange or other applications, as the Lync trunk cannot do any authentication on UAG – all authentication will be handled by the Lync Front End servers. Create a new HTTPS portal trunk and run through the wizard. Note that the trunk ‘Public host name’ must be a different name to any of the applications you are intending on publishing as we will be publishing whole domain names ‘/*’ and not just specific paths. Add authentication servers now and they will be disabled after the wizard completes.
Edit Trunk Authentication
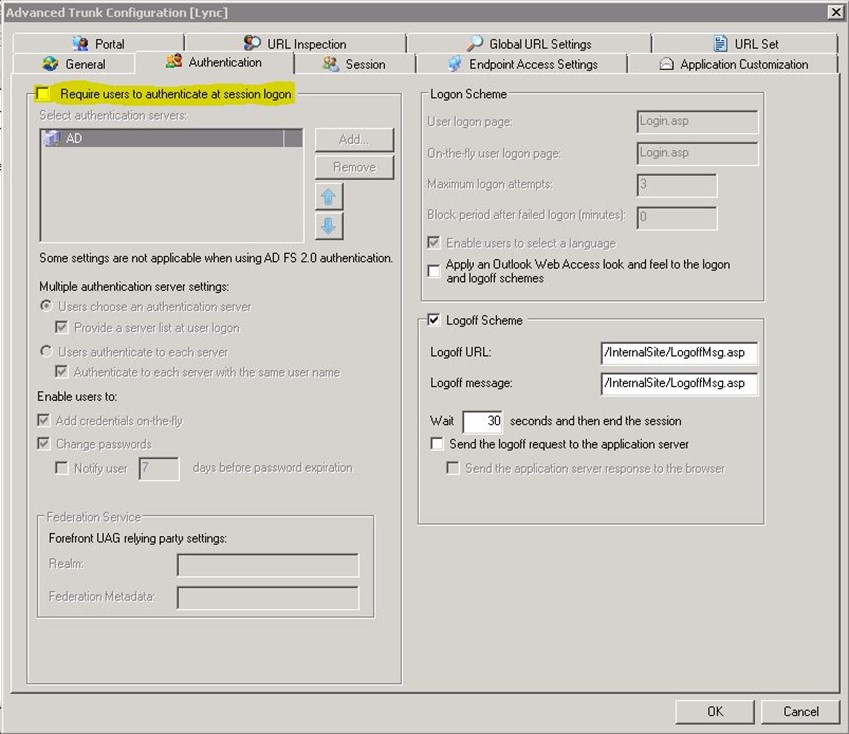
Configure the trunk and on the ‘Authentication’ tab, clear ‘Require users to authenticate at session logon’
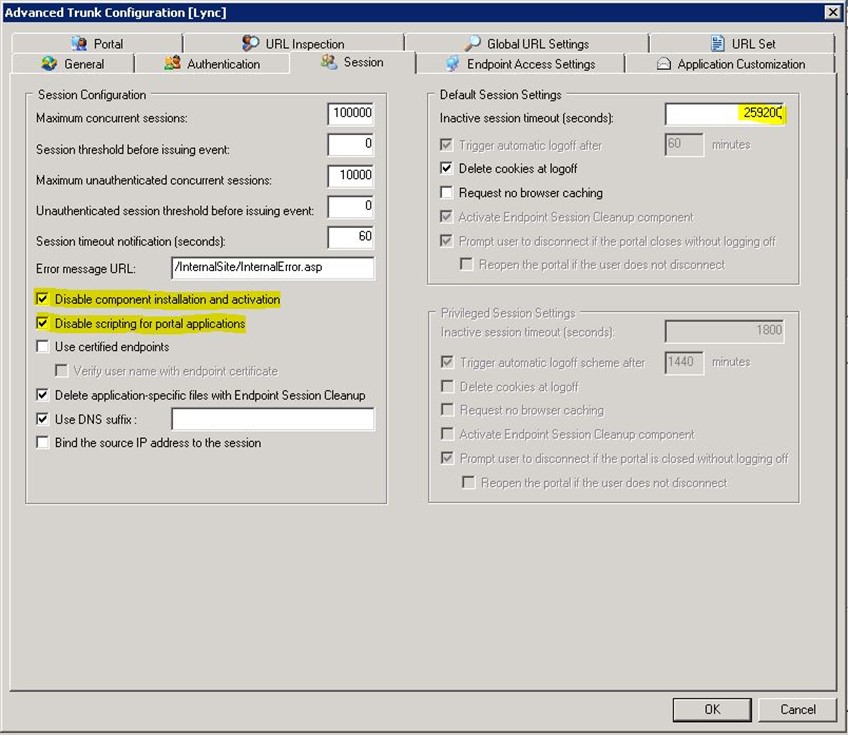
On the ‘Session’ tab, enable ‘Disable component installation and activation’ and ‘Disable scripting for portal applications’ to allow non supported browsers to connect. Increase the ‘Inactive session timeout (seconds)’ from the default 5 minutes to something closer to the 3 day (259200 seconds) ‘SessionExpirationInterval’ default for Lync 2013 as documented in Set-CsMcxConfiguration
Enable authentication pass through. UAG 2010 SP 3 defaults to having ‘FullAuthPassthru’ set to 1 in ‘HKEY_LOCAL_MACHINE\SOFTWARE\WhaleCom\e-Gap\von\UrlFilter’. For Lync to function we need another 32-bit DWORD key ‘KeepClientAuthHeader’ with a value of ‘1’ in the same location to retain the authentication headers.
Activate the trunk and go get a coffee while you wait for the activation process to complete and TMG storage to synchronise across all UAG array members.
Create Applications
Web Services
Create an application called ‘Lync 2013 Web Services’ using the ‘Microsoft Lync Web App 2010’ template. Follow the wizard and ensure you leave the path as ‘/’ and destination HTTPS port as ‘4443’. Uncheck ‘Use SSO’ and ‘Add portal and toolbar link’ and leave ‘Authorize all users’ enabled.
Three applications will be created as you can see below.
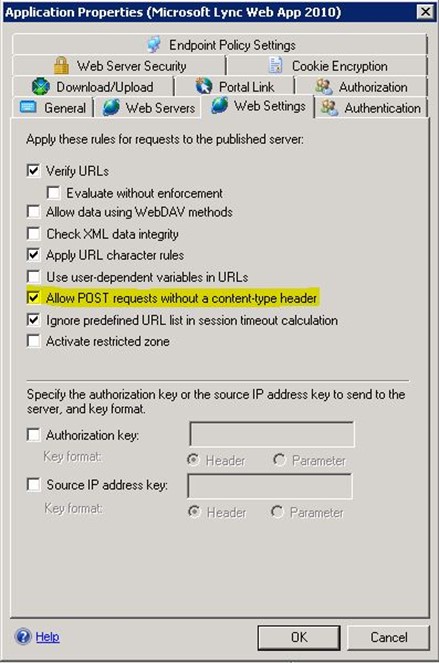
With the default configuration of Web Services, errors are posted in the UAG Web Monitor:
“A request for application Lync Web Services of type Lync2010 on trunk lync; Secure=1 failed because a POST action without a content-type header is not allowed. The URL is /WebTicket/WebTicketService.svc”
“A request for application Lync Web Services of type Lync2010 on trunk lync; Secure=1 failed because a POST action without a content-type header is not allowed. The URL is /ucwa/v1/applications/211401975557/me/reportMyActivity”
To allow Lync Mobile clients to authenticate to the Webticket service and update presence, edit the ‘Lync 2013 Web Services’ application and on the ‘Web Settings’ tab enable ‘Allow POST requests without a content-type header’.
Edit the meet and dialin applications and ensure ‘Addresses’ and ‘Public Host Name’ on the ‘Web Services’ tab are correct if you use different internal and external domain names. For readability I rename them to ‘Lync 2013 Meet’ and ‘Lync 2013 Dialin’.
Lyncdiscover
Create an application called ‘Lync 2013 Lyncdiscover’ using the ‘Microsoft Lync Web App 2010’ template with ‘Public Host Name’ ‘lyncdiscover.<sipdomain>’ and the same settings as the Lync Web Services application. Once the wizard is complete, remove the ‘Lync 2013 Lyncdiscover – Meet’ and ‘Lync 2013 Lyncdiscover – Dialin’ applications created by the rule.
Office Web Apps Server
Create an application called ‘Office Web Apps 2013’ using the ‘Microsoft Office SharePoint Server 2013’ template. Public host name should be the ExternalURL of the Office Web Apps Server Farm. Change the published port to ‘HTTPS’ port ‘443’ as it defaults to HTTP. As with the others, uncheck ‘Use SSO’ and ‘Add portal and toolbar link’ and leave ‘Authorize all users’ enabled.
Final Configuration
You should end up with an application list similar to this:
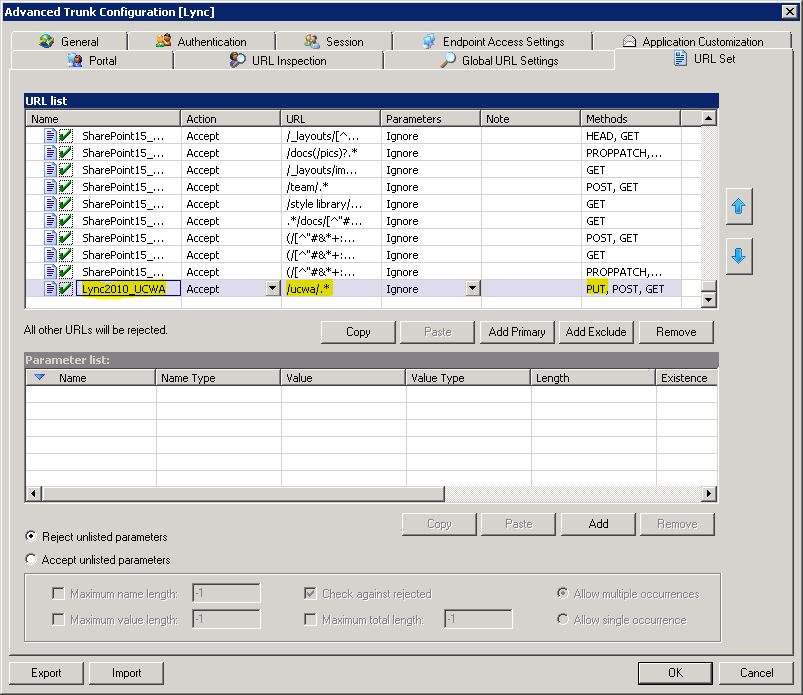
The final step is to edit the trunk to allow Lync Web App to upload and present presentations using Office Web App Server. The default configuration denies PUT requests for UCWA (Unified Communications Web API) and you receive ‘Invalid Method’ warning messages stating:
“A request from source IP address x.x.x.x, user on trunk lync; Secure=1 for application Lync Web Services of type Lync2010 failed because the method used PUT is not valid for requested URL /ucwa/v1/applications/111597367048/communication”
Configure the trunk settings and on the ‘URL Set’ tab, click ‘Add Primary’. Enter the following details:
Name: Lync2010_UCWA
Action: Accept
URL: /ucwa/.*
Parameters: Ignore
Methods: PUT, POST, GET
Close the trunk settings and activate the UAG configuration.
Testing
Considering the stated lack of support for Lync 2013 and specifically Lync Mobility, surprisingly all of the functions mentioned above worked without a hitch after the ‘POST without a content-type header’ and UCWA PUT issues were resolved. Lync 2013 and Lync 2010 mobile clients on Windows Phone, iOS and Android could sign in. Lync Windows Store App connects. Lync Web App worked beautifully including audio, video and content sharing. The Lync client could search the address book, join meetings and users could get dialin information and create Persistent Chat rooms. From our testing, everything is working as expected. I keep waiting for something to fail, but so far all is good.
I have been doing a lot of work with UAG lately and run into a lot of bugs and problems, so I think this may be the first of a few UAG blogs.
Edit 15 May 2013 – updated UCWA path.

Good work Marc. Keep it up.
I am doing the same thing in the LAB, only difference is, I am using TMG 2010 😉
There is no Microsoft Lync Web App 2010′ template in UAG 2010. Only office communicator web access 2007.
You need Service Pack 1 Update 1 installed to get the Lync 2010 template which I mention in the blog. This configuration is using Service Pack 3 as that adds the SharePoint 2013 template.
Great blog post, Marc. Thank you for the link to my blog post (I have since moved it to my New blog at WordPress). As you mention it has a few shortcomings, Things that were brought to my attention after the New mobile Client was released. I will check out the tips you have made to see if they can solve my problems!
Hi again Marc. I seem unable to get it working, even after applying SP3. I noticed the “typo” With the UCWA URL change, but that does not seem to have made any difference. I was aware of the POST header setting also, noticed it in the logs when we first Applied Lync 2013 mobile.
My scenario now is
– Lync 2013 mobile Works, but often reports server Connection error (but still Works)
– Lync 2013 mobile often gets double IM Messages
– Lync MX / Modern UI app is not able to Connect
– Office Web Apps server is available (replies With XML “jibberish” when accessing the /hosting/discovery URL) but only gives an error saying “Office Web Apps Server encountered an error” when trying to publish a presentation.
I cannot see any error in the logs on the UAG, neither on Front End WAC scenario logging. Have you really done this successfully?
Hi Rune. I have done it successfully in a development environment but haven’t gone into detailed testing. We are busy rebuilding in test and will shortly run through detailed test cases. I also get the connection error on the 2013 Android client, but get that when using TMG too and it still works. The Lync Windows Store App (MX / Modern UI) does work (and you made me realise I hadn’t listed it in the requirements so I have updated it now).
I didn’t have any issues with the Office Web Apps Server. If the ‘jibberish’ you mention is valid XML with the WOPI endpoints that match what you are publishing, that should be all the UAG configuration you need. Does PowerPoint sharing work internally? Do get-officewebappsfarm and get-officewebappsmachine show valid configuration? I don’t know if it matters, but our OWAS InternalURL and ExternalURL are the same so my UAG ‘Public host name’ and ‘Addresses’ have the same name.
Hi again Marc, and sorry about the delayed response.
The “jibberish” is just what you described, the XML WOPI configuration. Still didn’t work, so I went back to the pre UAG SP1 solution to unbind the HTTP listener IP’s from UAG’s grasp, and rather publish Lync Web Services and OWAS through TMG part of the UAG. Unsupported, I know, but now everything Works smoothly.
For my part I will defer the future use of UAG for Reverse Proxy where Lync is involved, until Microsoft officially declares the support for it.
Cheers!
-Rune