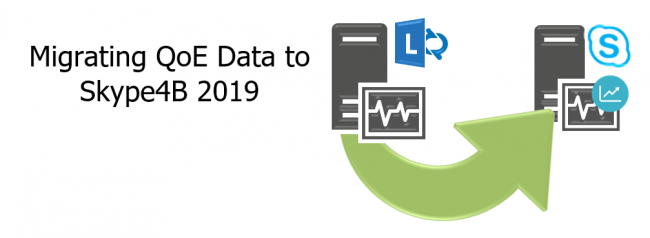
Upgrade existing Lync/Skype QoE data to Skype for Business 2019
Skype for Business 2019 is the latest and greatest on-premises UC product from Microsoft, and if you are deploying it in an existing environment as part of your journey to the cloud you may have some legacy call data in your Lync 2013 or Skype for Business 2015 servers. In this guide, we take a look at how to import that existing data into our new Skype for Business 2019 deployment.