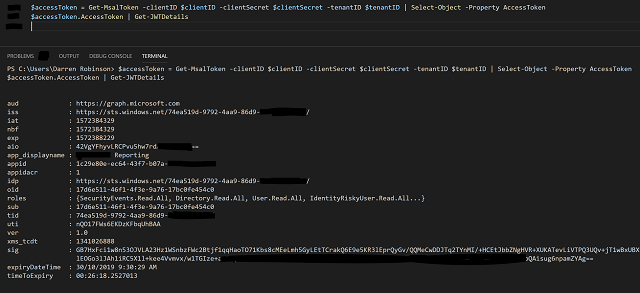
Microsoft Graph using MSAL with PowerShell
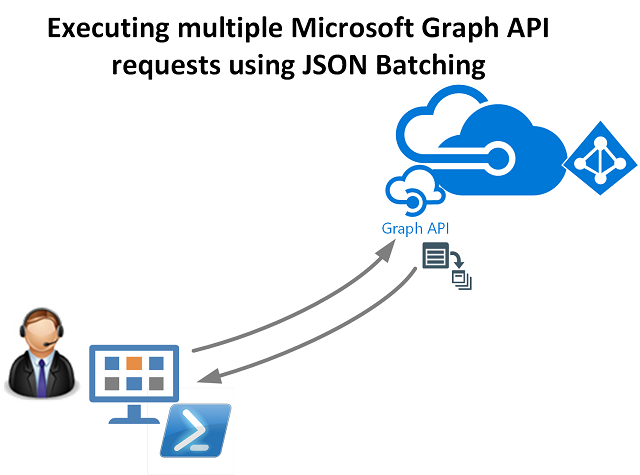
Microsoft Authentication Libraries (MSAL) became Generally Available in May 2019 after a very long preview cycle whilst the libraries evolved to reach parity with its predecessor the Azure Active Directory Authentication Libraries (ADAL). I’ve previously used and written posts on leveraging ADAL libraries with PowerShell for Azure AD/Microsoft Graph integration using PowerShell. With some upcoming projects it’s time for me to start integrating with Microsoft Graph using MSAL with PowerShell. This post details how I transitioned from ADAL to MSAL and reduced my scripts by 60-300 lines depending on the integration.… [Keep reading] “Microsoft Graph using MSAL with PowerShell”