Deploying a SailPoint IdentityNow Virtual Appliance in Azure
Introduction
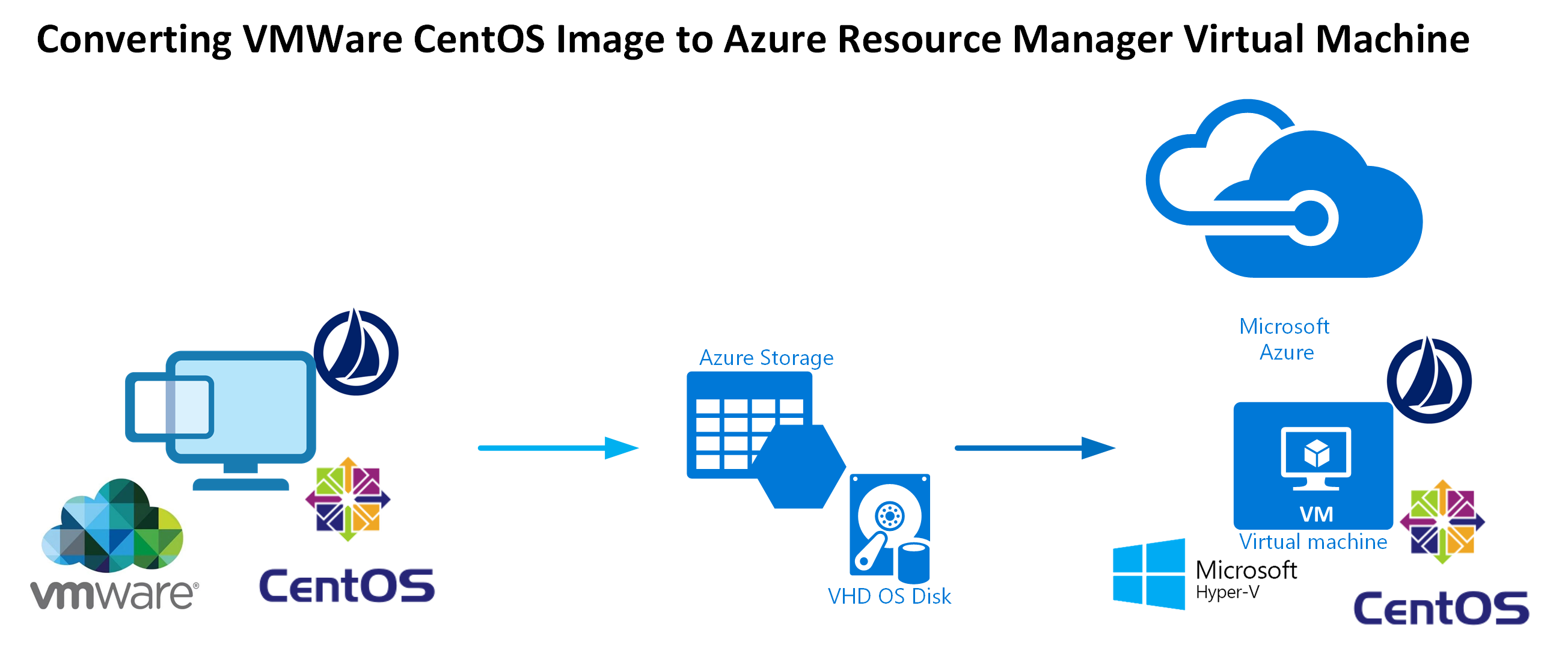
The CentOS image that SailPoint provide for the IdentityNow Virtual Appliance that performs integration between ‘Sources’ and IdentityNow is VMWare based. I don’t have any VMWare Infrastructure to run it on and really didn’t want to run up any VMWare environments for this component. All my other infrastructure is in Azure. I’d love to run my VA(s) in Azure too.
In discussions with SailPoint I understand it is simply a case that they haven’t certified their CentOS image on Azure.… [Keep reading] “Deploying a SailPoint IdentityNow Virtual Appliance in Azure”