Overcoming Issues Installing Azure Active Directory Connect
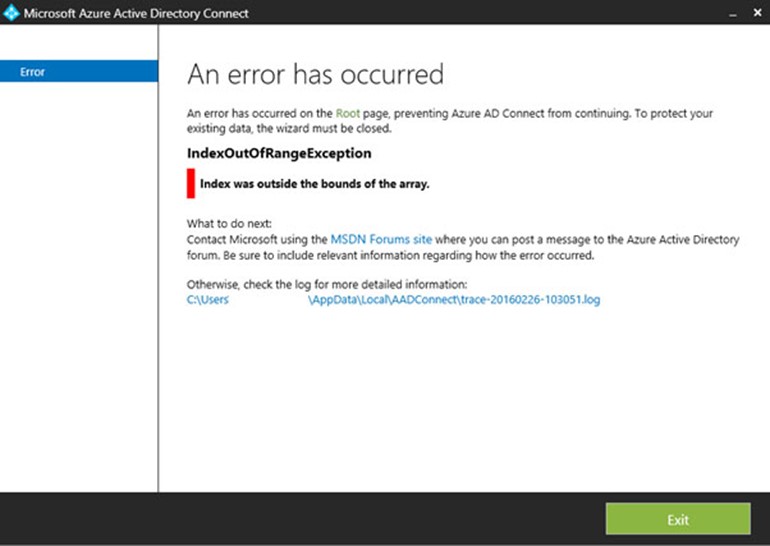
Having recently gone through the process of implementing a custom AADConnect staging installation for a large enterprise customer with more than 30,000 users, with a view to it serving as a fall back to an existing production AADConnect installation.
The requirement being to setup an Azure virtual machine running Windows 2016 Datacentre, AADConnect and SQL Server Standard 2017 (locally installed). Rather than SQL Express which comes by default but suffers limitations which preclude its use in large environments.… [Keep reading] “Overcoming Issues Installing Azure Active Directory Connect”