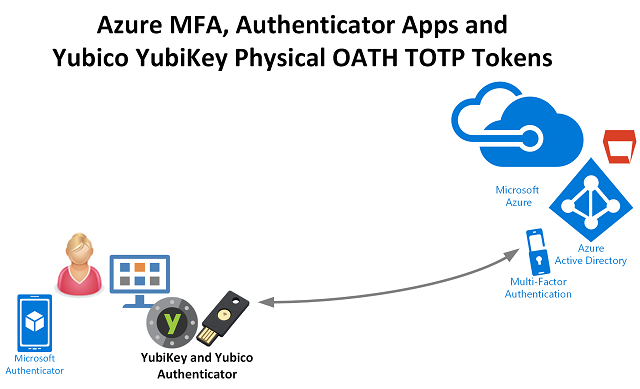
An Azure MFA Management Agent for User MFA Reporting using Microsoft Identity Manager
Microsoft as part of the uplift in Authentication Methods capability have extended the Graph API to contain User Azure MFA information. My customers have been requesting MFA User Reporting data for some time. How many users are registered for Azure MFA? What and how many methods are they registered with? The new Graph API functions provide this information and we no longer have to use the legacy MSOLUser PowerShell cmdlet to obtain the strongAuthenticationMethods information. The new API’s provide;
- self-service password reset and multi-factor authentication (MFA) information for all registered users
- how many users in your organization are registered for self-service password reset and multi-factor authentication capabilities
Azure MFA User Reporting Management Agent
With this new functionality exposed, I’ve built an Azure MFA Management Agent for Microsoft Identity Manager to consume information from the credentialRegistrationDetails API, which can then be used in Identity Workflows to trigger notifications to users that don’t have enough registered methods (e.g.… [Keep reading] “An Azure MFA Management Agent for User MFA Reporting using Microsoft Identity Manager”