Introduction
As an Identity Management consultant if I had a $1 for every time I’ve been asked “what is user x’s current status in IDAM”, “is user x active?”, “does user x have an account in y?”, “what is user x’s primary email address?”, particularly after Go Live of an IDAM solution my holidays would be a lot more exotic.
From a Service Desk perspective IDAM implementations are often a black box in the middle of the network that for the most part do what they were designed and implemented to do. However as soon as something doesn’t look normal for a user the Service Desk are inclined to point their finger at that black box (IDAM Solution). And the “what is the current value of ..”, “does user x ..” type questions start flying.
What if we could give the Service Desk a simple query interface into FIM/MIM without needing to give them access to another complicated application?
This is the first (of potentially a series) blog post on leveraging community libraries and Azure PaaS services to provide visibility of FIM/MIM information. This first post really just introduces the concept with a working example in an easy way to understand and replicate. It is not intended for production implementation without additional security and optimisation.
Overview
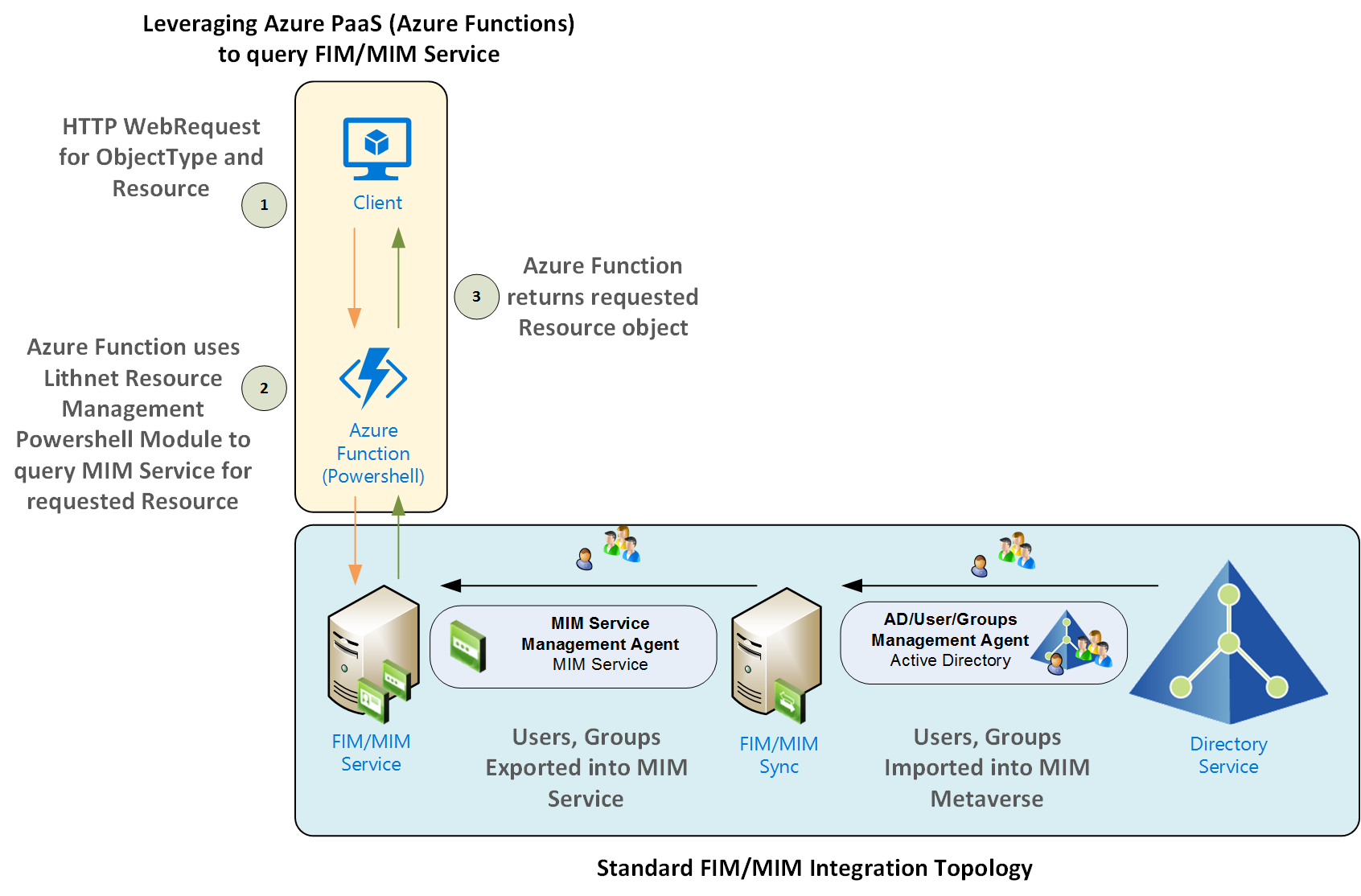
The following graphic shows the concept of using Azure Functions to take requests from a client (web app, powershell, some other script) query the FIM/MIM Service and return the result. This post details the setup and configuration for the section in the yellow shaded box with the process outlined in the numbers 1, 2 & 3. This post assumes you already have your FIM/MIM implementation setup and configured according to your connected integrated applications/services such as Active Directory. In my example my connected datasource is actually Twitter.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/Solution%20Arch.png
Prerequisites
The prerequisites for this solution are;
- An Azure Tenant
- FIM/MIM Portal Service (as per the diagram above)
- I’ll also be using the awesome Lithnet Resource Management Powershell Module for Microsoft FIM/MIM from Ryan Newington. A fantastic contribution to the FIM/MIM community
Creating your Azure App Service
First up you’ll need to create an Azure App Service in your Azure Tenant. To keep everything logically structured for this example I created an Azure App Service in the same resource group that contains my MIM IaaS infrastructure (MIM Sync Server, MIM Service Server, SQL Server, AD Domain Controller etc).
In the Azure Marketplace select New (+) and search for Function App. Select the Function App item from the results and select Create.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/New%20Function%20App.png
Give your Azure App Service a name, choose the Resource Group where you want to locate it. Choose Dynamic for the Hosting Plan. This means you don’t have to worry about resource management for your Web App and you only pay for execution time which unless you put this into production and have gone crazy with it your costs should be zero as they will (should) be well under the free grant tier. Put the application in the appropriate location such as close to your FIM/MIM resources that it’ll be interacting with and select Create.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/CreateFunctionApp.png
Now that you have your Azure App Service setup, you need to create your Azure Function.
Create an HTTP Trigger Powershell Function App
In the Azure Portal locate your App Services Blade and select the Function App created in the steps above. Mine was named MIMMetaverseSearch in the example above. Select PowerShell as the Language and HttpTrigger-Powershell as the Function type.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/Create%20HTTP%20Trigger%20Function%20App.png
Give your Function a name. I’ve kept it simple in this example and named it the same as my App Service Plan. Select Create.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/Create%20Function%201.png
Adding the Lithnet Powershell Module into your Function App.
As you’d expect the Powershell Function App by default only has a handful of core Powershell Modules. As we’re using something pretty specific we’ll need put the module into our Function App so we can load it and use the library.
Download and save the Lithnet Resource Management Powershell Module to your local machine. Something like the Powershell command below will do that.
Next follow this great blog post here from Tao to upload the Lithnet RMA PS Module you downloaded earlier into your function directory. I used WinSCP as my FTP client as I’ve shown below to upload the Lithnet RMA PS Module.
FTP to the host for your App Service and navigate to the /site/wwwroot/
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/FTP%20to%20Functions%20Directory.png
Create a bin folder and upload via FTP the Lithnet RMA PS Module.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/PS%20Module%20Uploaded.png
Using Kudu navigate to the path and version of the Lithnet RMA PS Module.
I’m using v1.0.6088 and my app is named MIMMetaverseSearch so MY path is D:\home\site\wwwroot\MIMMetaverseSearch\bin\LithnetRMA\1.0.6088
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/Kudu%20Path%20to%20module.png
Note: the Lithnet RMA PS Module is 64-bit so you’ll need to configure your Web App for 64-bit as per the info in the same blog you followed to upload the module here.
Test loading the Lithnet RMA PS Module in your Function App
In your Function App select </> Develop. Remove the sample script and in your first line import the Lithnet RMA PS Module using the path from the previous step. Then, to check that it loads add a line that references a cmdlet in the module. I used Help Get-Resource. Select Save then Run.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/Simple%20Load%20and%20Test%20Function.png
If you’ve done everything correct when you select Run and look at the Logs you’ll see the module was loaded and the Help Get-Resource command was run in the Logs.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/LithNET%20RMA%20PS%20Module%20Loaded.png
Allow your Function App to access your FIM/MIM Service Server
Even though you have logically placed your Function App in the same Resource Group (if you did it like I have) you’ll need to actually allow the Function App that is running in a shared PaaS environment to connect to your FIM/MIM Service Server.
Create an inbound rule in your Network Security Group to allow access to your FIM/MIM Service Server. The example below isn’t as secure as it could (and should) be as it allows access from anywhere. You should restrict the source of the request(s) accordingly. I’m just showing how to quickly get a working example. TCP Port 5725 is required to access your MIM Service Server. Enter the details as per below and select Ok.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/InboundNSG%20Rule%20-%20FIM%20Service.png
Using an Azure Function to query FIM/MIM Service
Note: Again, this is an example to quickly show the concept. In the script below your credentials are in the script in clear text (and of course those below are not valid). For anything other than validating the concept you must protect your credentials. A great example is available here in Tao’s post.
The PS Azure Function gets the incoming request and converts it from JSON. In my request which you’ll see in the next step I’m passing in “displayName” and “objectType”.
In this example I’m using Get-Resource from the Lithnet RMA to get an object from the FIM/MIM Service. First you need to open a connection to the FIM/MIM Service Server. On my Azure IaaS MIM Service Server I’ve configured a DNS name so you can see I’m using that name in line 17 to connect to it using the unsecured credentials from earlier in the script. If you haven’t set up a DNS name for your FIM/MIM Service Server you can use the Public IP Address instead.
Line 20 queries for the ObjectType and DisplayName passed into the Function (see calling the Function in the next step) and returns the response in line 22. Again this is just an example. There is no error checking, validation or anything. I’m just introducing the concept in this post.
Testing your Function App
Now that you have the function script saved, you can test it from the Function App itself. Select Test from the options up in the right from your function. Change the Request Body for what the Function is expecting. In my case displayname and objectType. Select Run and in the Logs if you’ve got everything configured correctly (like inbound network rules, DNS name, your FIM/MIM Service Server is online, your query is for a valid resource) you should see an object returned.
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/TestFunction.png
Calling the Function App from a Client
Now that we have our Function App all setup and configured (and tested in the Function App) let’s send a request to the Azure Function using the Powershell Invoke-RestMethod function. The following call I did from my laptop. It is important to note that there is no authN in this example and the function app will be using whatever credentials you gave it to execute the request. In a deployed solution you’ll need to scope who can make the requests, limit on the inbound network rules who can submit requests and of course further protect the account credentials used to connect to your FIM/MIM Service Server.
Successful Response
The following screenshot shows calling the Function App and getting the responding object. Success. In a couple of lines I created a hashtable for the request, converted it to JSON and submitted it and got a response. How powerful is that!?
https://dl.dropboxusercontent.com/u/76015/BlogImages/MIMFunctionApp/Response.png
Summary
Using the awesome Lithnet Resource Management PowerShell Module with Azure Functions it is pretty quick and flexible to access a wealth of information we may want to expose for business benefit.
Now if only there was an affiliation program for Azure Functions that could deposit funds for each IDAM request to an Azure Functions App into my holiday fund.
Stay tuned for more posts on taking this concept to the next level.
Follow Darren on Twitter @darrenjrobinson
